(Please note this post was originally published in the Spanish version of Security Art Work last 20th Jul 2011)
This post is not about steganography (see the definition we did in another post — Spanish), nor any complex technique developed by a technology expert. This is something much simpler: the geolocation information that some devices —including many smartphones— store on the photos without many users being aware of it. That information is saved in the “hidden” information of the photos and can be easily accessed with programs such as exif reader. Please note that with “hidden information” we do not mean information someone has tried to hide, but information that is unknown to most users of smartphones what in practice is basically the same as what we understand by “hidden”. Usually these devices have an option that allows us to enable or disable geolocation features; for instance, to do so on the Blackberry there is an option called GeoTag in the camera options.
As always the fact that a smartphone can geotag a photo is not a good or bad thing by itself. Our use of this information it’s what makes it a potential hazard so it’s important that everyone, especially the youngest ones, are aware of such information. It must be taken into account that the mixture between the geolocation of a photo and real-time information systems as it is the case of twitter can become an explosive mixture.
We can get an idea of this by visiting the url http://icanstalku.com/ (project currently closed). It’s just scaring.
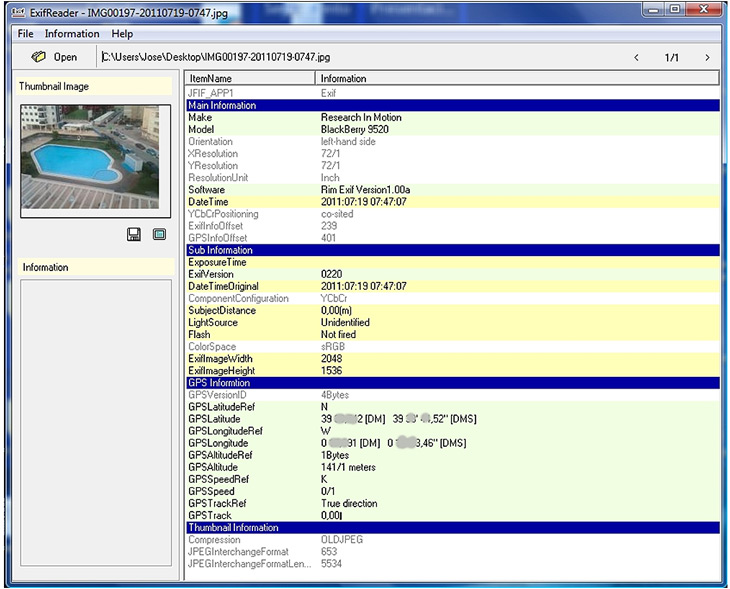
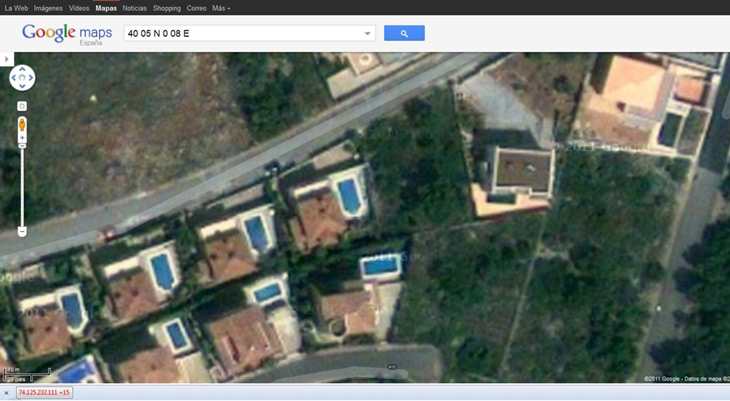
As we can see, extracting the geolocation data (longitude and latitude stored in the photo information) and using Google Maps we have not only the picture of our beautiful dog that we wanted to share with our friends but also the geolocation of our nice house:
What follows it is a fictional story… or maybe not.
Let’s suppose “bichomalo” (if you want to know who “bichomalo” —Badguy— is check this link: http://www.youtube.com/watch?v=JcB_RfX0BVQ — Spanish) has just found Alice, a nice 15 years old girl who he is obsessed with.
Girl dads’ have bought her the latest smartphone with an Internet flat rate; they don’t know much about technology or security risks. Alice creates her twitter user —of course with her real name— and begins to tweet; it is cool. Soon, she starts sharing photos in their tweets, ignoring that they contain the coordinates of the place where the photo is taken. Bichomalo certainly knows it. He creates a fake profile and follows the girl; a photo of a young blonde girl trimmed down to show only her eyes, downloaded from any corner of the Internet, makes it credible enough. He often tweets girly things and even sends some private messages to Alice.
This friday our girl is at the birthday of her best friend. It took she some time to convince her parents but they finally accepted because she would not be far from home. The party is funny and she tweets many photos, but at 2am she gets tired and decides to go back home, only a few blocks away. “Time 2 go home“, publishes Alice in her twitter… Bichomalo reads it and knows exactly where is she, where is she going and her way to home; almost a hundred photos published over a couple of months with a lot of geolocation data. We don’t need to say anything else.
We can’t deny geolocation it is a useful technology. However, as with any other technology, we must be aware of its dangers and there’s only one way for it: education. Even more when, as we have seen, when its bad use may impact significantly on vulnerable groups as our children.
