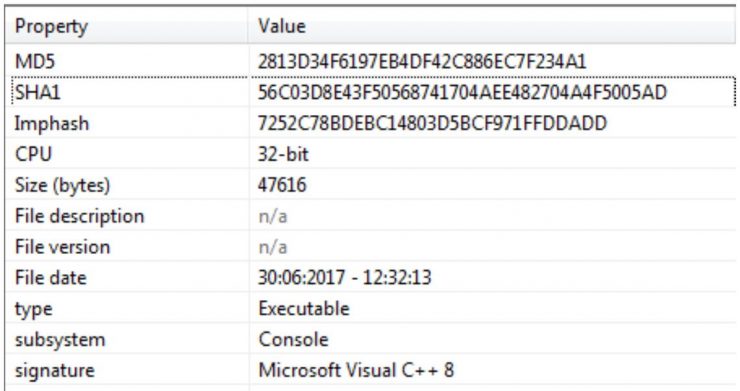
We continuously receive phishing emails coming from a variety of sources, often containing attachments with malicious payloads. In this case the attachment was a bit more interesting because it embedded a .docm file inside a .pdf file.
The email that arrived to our servers had “Order” as subject, and no visible content, only a p(paragraph) HTML entity with an empty symbol, but fun was on the attachment.
Attack stages
The attachment was a proper PDF file that contained a .docm file embedded. Once you opened the pdf file de docm would unpack and execute its macros leading to the download of a file that, once repacked by the macro on execution, would be executed in the system.
[Read more…]

 From the malware lab of S2 Grupo we have been monitoring the movements of a Trojan known as Trickbot. Its relationship with Dyre, another older Trojan with which it shares many design features, and the speed at which it evolves, has captured our interest ever since we saw the first samples.
From the malware lab of S2 Grupo we have been monitoring the movements of a Trojan known as Trickbot. Its relationship with Dyre, another older Trojan with which it shares many design features, and the speed at which it evolves, has captured our interest ever since we saw the first samples. I do not think it necessary to mention what the SSH (Secure Socket Shell) protocol is, since it would be really difficult to live without it today. Therefore, SSH is considered globally as the “mega” indispensable tool for any administration work. Among the advantages of its use we can find: secure access to remote machines, access to services on other machines by creating direct or reverse tunnels, creation of proxy socks, creation of secure channels for the encapsulation of traffic from unsecured applications … etc.
I do not think it necessary to mention what the SSH (Secure Socket Shell) protocol is, since it would be really difficult to live without it today. Therefore, SSH is considered globally as the “mega” indispensable tool for any administration work. Among the advantages of its use we can find: secure access to remote machines, access to services on other machines by creating direct or reverse tunnels, creation of proxy socks, creation of secure channels for the encapsulation of traffic from unsecured applications … etc. We have talked so far about the main services that make up the Russian intelligence community in its cyber domain and we will continue to describe in successive posts the rest of the complex Russian ecosystem but, where are the allegedly Russian APTs? Groups known to everyone, such as APT28 (FancyBear, Sofacy …) or APT29 (CozyBear, The Dukes …), must be somehow related to this community … if they are not part of it, right?
We have talked so far about the main services that make up the Russian intelligence community in its cyber domain and we will continue to describe in successive posts the rest of the complex Russian ecosystem but, where are the allegedly Russian APTs? Groups known to everyone, such as APT28 (FancyBear, Sofacy …) or APT29 (CozyBear, The Dukes …), must be somehow related to this community … if they are not part of it, right? The only major Russian service which, as we have indicated, is not a direct heir of the KGB is the GRU (Glavnoye Razvedyvatelnoye Upravlenie), military unit 44388, whose aim is to provide intelligence to the Ministry of Defense, the military leadership and Russian armed forces as a whole. This service is dedicated to military intelligence, from strategic to operational, working not only in an exclusive sense of defense, but also encompassing other aspects such as politics or economy linked to the military sphere, and especially foreign intelligence – sometimes with the SVR. Since 1996, it has been entrusted with the mission of acquiring information on ecology and the environment. In order to execute these tasks, the GRU has all kinds of capabilities, from IMINT to HUMINT, through OSINT and, of course, SIGINT, capabilities that give it a sphere of action and international influence and that allow the GRU to “act in any point of the world where the need might arise, “according to statements by General Valentin Vladimirovich Korabelnikov, in an interview granted in 2006, when he was Director of GRU.
The only major Russian service which, as we have indicated, is not a direct heir of the KGB is the GRU (Glavnoye Razvedyvatelnoye Upravlenie), military unit 44388, whose aim is to provide intelligence to the Ministry of Defense, the military leadership and Russian armed forces as a whole. This service is dedicated to military intelligence, from strategic to operational, working not only in an exclusive sense of defense, but also encompassing other aspects such as politics or economy linked to the military sphere, and especially foreign intelligence – sometimes with the SVR. Since 1996, it has been entrusted with the mission of acquiring information on ecology and the environment. In order to execute these tasks, the GRU has all kinds of capabilities, from IMINT to HUMINT, through OSINT and, of course, SIGINT, capabilities that give it a sphere of action and international influence and that allow the GRU to “act in any point of the world where the need might arise, “according to statements by General Valentin Vladimirovich Korabelnikov, in an interview granted in 2006, when he was Director of GRU. Another of the heirs of the FAPSI is the FSO (Federal’naya Sluzhba Okhrani), identified in [1] as military unit 32152 and headed since May of this year by Major General Dmitry Kochnev (his predecessor, Evgeny Murov, was General of the Army, two ranks higher, and this in the Russian services is very important). Murov obtained very important FAPSI attributions: with more than 20,000 troops today (supposedly, since it is classified information, and various sources speak of more than 50,000), the FSO inherited and expanded the KGB’s Ninth Address, with responsibility for the protection of governmental “goods”, in the broadest sense of the word. For example, the Presidential Security Service, the PBS-Putin’s bodyguards, or control of the famous Russian nuclear briefcase depend on the FSO, as well as the operation of a secure network for the transmission of election results,
Another of the heirs of the FAPSI is the FSO (Federal’naya Sluzhba Okhrani), identified in [1] as military unit 32152 and headed since May of this year by Major General Dmitry Kochnev (his predecessor, Evgeny Murov, was General of the Army, two ranks higher, and this in the Russian services is very important). Murov obtained very important FAPSI attributions: with more than 20,000 troops today (supposedly, since it is classified information, and various sources speak of more than 50,000), the FSO inherited and expanded the KGB’s Ninth Address, with responsibility for the protection of governmental “goods”, in the broadest sense of the word. For example, the Presidential Security Service, the PBS-Putin’s bodyguards, or control of the famous Russian nuclear briefcase depend on the FSO, as well as the operation of a secure network for the transmission of election results,