Several months ago (october 2013, if I recall correctly), I found some vulnerabilities on an HMI from OMRON. I wrote a post in Spanish describing the almost endless process we went thru from the discovering of the vulnerability to its publication (you can check the automatic Google translation here, though I assume no responsability).
Ten months later, we got the green light from OMRON (with great work by ICS-CERT and other CERTs), probably mostly pressed by our decission to publish the vulnerability at mid-end July. Lucky we’re the good guys. Now the vulnerability has been released: Advisory (ICSA-14-203-01), Omron NS Series HMI Vulnerabilities, so let’s go with the (few) details.
The following vulnerabilities were found in the NS15 version 3.19 (I do not know if other versions are affected), an HMI from OMRON.
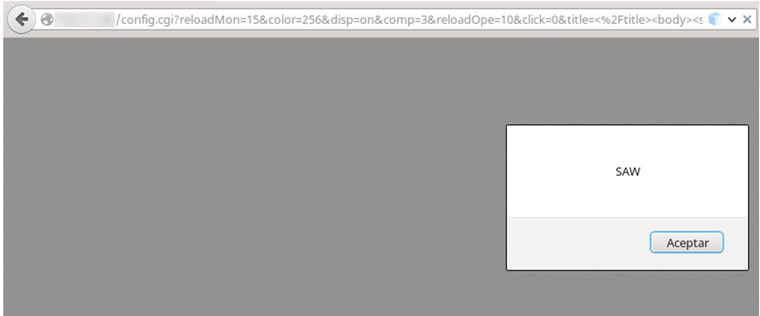
The first is a persistent XSS that would allow the attacker inject malicious code through the configuration form, particularly in the parameter “Page Title”, which is responsible for changing the title of the web pages in the system. However, to take advantage of it, the attacker must be authenticated to the system. However, that’s not all, folks.
When the webpage wants to store the changes made, it submits the values with a “GET” HTTP command, revealing all the options and their values in the navigation bar. As it doesn’t exist any token, an attacker could exploit this CSRF vulnerability by creating a malicious URL to make changes in the HMI configuration.
Although at first both vulnerabilities may seem rather simple and even irrelevant, if exploited in a critical system the results could be devastating.
Imagine that an attacker decides to make an attack on the operator that is responsible for controlling the HMI system. To do this, the attacker will send a link, taking advantage of the CSRF, to inject a payload that leverages the XSS vulnerability. In this case, the purpose of the payload will be to change the HMI control webpage values.
This way, the attacker could get the operator to apply changes to the system based on false information (chosen by the attacker for their own purposes). In another scenario, if the attacker attacks successfully the system, it would be invisible to the operator, who would see everything in perfect condition.
