Ransomware is here to stay. This is something becoming clearer by the minute. It is a very lucrative business if we judge it by the successful infection effectiveness rate and, to a lesser extent, due to rescue payment rates by the affected parts.
To the already infamous Cryptolocker, CryptoWall, TorrentLocker, TeslaCrypt and others, we have to add the recent HydraCrypt and UmbreCrypt. All of them with slight variations over the previous ones in an attempt to avoid the scarce barriers that Antivirus institutions are introducing, together with some initiatives more or less imaginative, and somewhat effective, in order to identify the activity of this kind of threat.
Recently, the CNI (Spanish National Intelligence Center), through the CCN-CERT, published a Ransomware guide where they had compiled some ransomware variants together with file decrypting tools that different Antivirus companies provided, after disarticulating several criminal networks or after deep analysis of malware samples.
In order to avoid being a victim of this menace, we highlight the usual recommendations:
-
Do not open attached documents in emails from unknown people.
-
Do not open attached documents in emails from known people whose content is not usual.
-
Keep your software up to date in order to avoid infection while browsing the Internet.
-
And above all, and most useful as we show below, do not login the systems with administrator rights unless necessary.
This last advice, even though is recommendable due to any other reasons, is the last line of defense against this kind of threats. Why do I say this? Because when the user’s common sense prudence fails when he opens suspicious files, when the Antivirus fails to recognize the menace, and when whatever network protection measures that could be there in order to forbid the access to malicious servers fail, only the user rights at that machine can allow the recovery of the encrypted files.
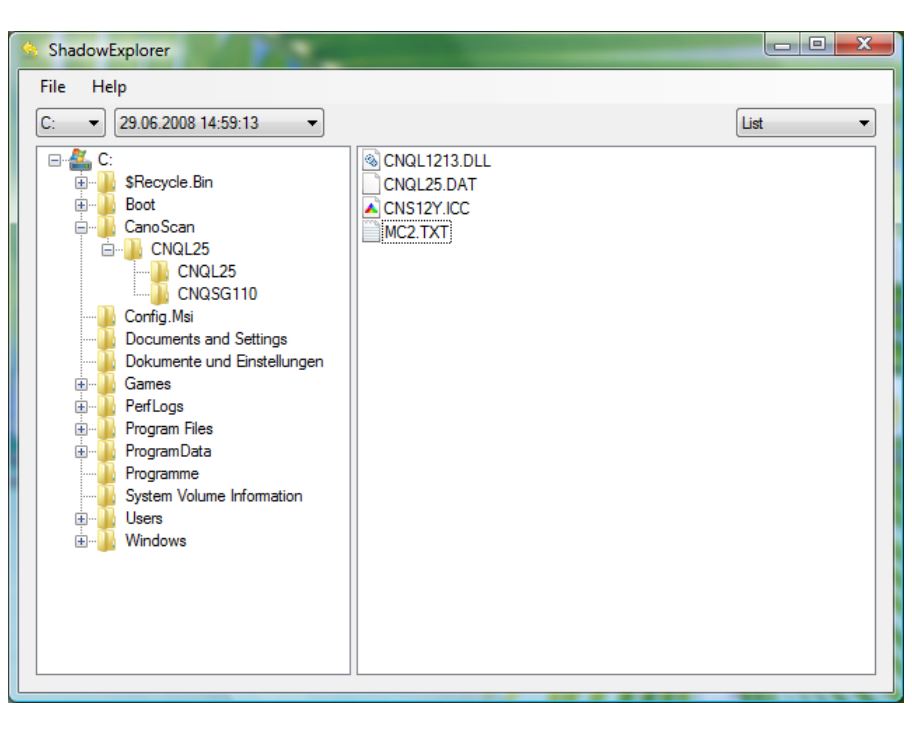
Most of this variants, when they encrypt a file, what they do is to create a new encrypted file based on the original. The reality is that the original file is erased and, in most cases, overwritten several times with ones and zeros in order to make the recovery impossible through file recovery tools. As criminals know the procedure, they discovered some time ago that through the default configured Volume Shadow Copies on Windows it is possible to recover the deleted files. Therefore they focused on disabling and eliminating this copies. Indeed, the CNI indicates them as unique alternative to backup copies and, in case of no availability of recovery tools, the use of Shadow Explorer, an application that dives into this automatic copies in order to find our encrypted files.
As I said, the criminals know this and the very first thing that most of the ransomware does when it executes inside a system is to eliminate the copies with the next command:
vssadmin.exe Delete Shadows /all /quiet
In order to successfully execute this, administrator rights are required, therefore our copies will be protected if we do not have this rights and we are able to recover our files with Shadow Explorer.
Finally, remember that the Volume Shadow Copy comes activated by default only in the C unit, the OS unit, therefore if we have other units mapped into the system where the local files of the user are being stored, it is convenient to activate this service in those other units.
Lets take down the myth that ransomware only affects to network units mapped in the affected hardware. It has been a while since numerous ransomware variants scan the local network looking for shared resources where the user has write permissions so it can encrypt those files also. Consequently, we should consider activating the Volume Shadow Copy service also in this devices.
(Translated from Spanish by Víctor Fernández Escorihuela)
