Blockchain. Maybe some of you have heard of it. Others maybe not. Inside some circles, Blockchain is a concept that is resonating with force, even though a fair amount of people does not comprehend exactly what it is or why it is important. Any of us could ask: What is a blockchain?
Let’s read the definition from a random corner of the Internet: “A blockchain is a chain of blocks that contains batches of valid transactions. Each block includes the hash of the previous block of the blockchain, linking the two. The linked blocks form a chain, allowing only that block (successor) to be linked only to the other block (predecessor), giving its name to this database”.
Therefore, we could say that a blockchain is a chain of data blocks that contain transactions. Well, it doesn’t seem a promising thing, does it?
Let me highlight a little detail: a blockchain is a ledger of transactions that can’t be manipulated, nor forged. Can you imagine what we could do with this?
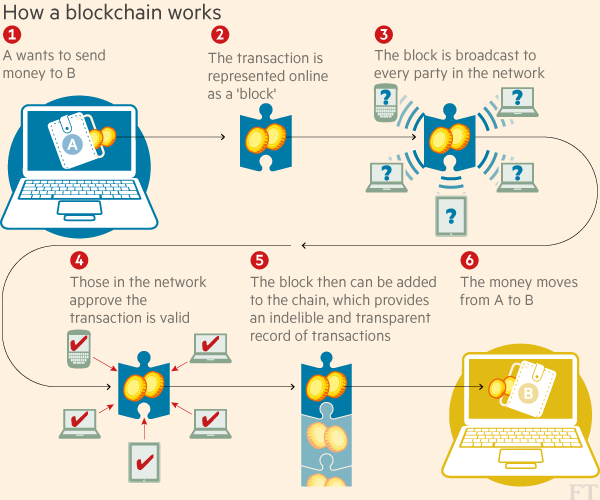
This first definition talks about the cornerstone of this technology, however, the blocks are just the beginning. In this “transaction ledger” that is a blockchain, the blocks that contain the information about the transactions are distributed over the Internet to all the nodes that compose the network. Those nodes process the information and reach a consensus, then they validate the transaction and add the block to the chain, leaving an undeletable and public registry of the transaction.
We can see in the next image a more visual explanation of how the blockchain works using the most common case to date: Monetary transactions.
The first and very valid question that arises is: and who are those nodes?
Everyone can be a node. All the blockchain code is Open Source and can be executed in any computer. The key to success resides on the motivation for being a node. The anonymous father of the blockchain, Satoshi Nakamoto, very intelligently integrated a reward mechanism for the nodes in the validation process of the transactions.
In order to validate a block, the network has to reach a consensus through a well-known mechanism. The most used and polished is “proof of work”, even though others exist. This mechanism is based on the properties of some algorithms, like, for example, finding a hash, for which it is quite hard (in time and computational resources) to solve certain arbitrary problems, but it is quite easy to check if the solution is correct.
In order to add a block to the chain, the nodes must select a certain quantity of transactions from a pool, check that they are valid, retransmit them, and calculate the proof of work over all the block of transactions, whose solution must comply with several requirements. To find this proof of work is a random process with a probability directly proportional to the computational resources used as a lot of trial and error is required on average until a solution is found.
The first node that finds a solution is rewarded. In some way, the nodes are competing against each other. In the Bitcoin case, the reward consists of a fixed Bitcoin quantity, and some fee that the transaction creators can add in order to encourage the nodes to include the transaction in their block as soon as possible.
When a node forges a valid block, it is retransmitted to the rest of the network, that check the validity of this block and the transactions that it contains, based on the blocks (previous transactions) that are already inscribed in the blockchain.
As the transactions are validated for each block, the only way of successfully performing a “double spend attack”, in order to spend twice the same coin, it is necessary to rewrite all the blocks from the transaction that we are trying to manipulate to the last block added.
This is why the more blocks a transactions has behind, the more secure a transaction is considered. For important transactions in Bitcoin, for example, a depth of six blocks (around one hour) is considered as absolutely impossible to manipulate.
Even though at first glance it may appear that this is a toy process, the complexity of the inherent security mechanisms in this technology is awesome, attracting an incredible community of developers and cryptographic experts that have been working on it since Satoshi Nakamoto, somewhere around 2009, published its genial Whitepaper.
Does this appear as something revolutionary?
The truth is that it is. This consensus mechanism has great implications. As there is no “official” copy and any particular node is trusted more, we can talk about a decentralized trust system.
And this is the main course.
The first blockchain application is more known than the technology itself: Bitcoin. And for several years, it has been its only application. However, around 2014, what is known as blockchain 2.0 technologies began to emerge. These are a new wave of applications based on the blockchain, because the chain is able to register more types of data other than transactions.
This data can be anything. From legal birth certificates, weddings, cadastral registries or digital identities, going through copyrights (with first creation proof), patents or even have votes or contracts.
Traditionally, a central authority in which everyone trusts has been necessary in order to ensure that a piece of information (a document) is valid and trustworthy. This is the purpose of a lot of entities: Notaries, banks, several administrations and public registries, dispute resolution systems … And, this is so that the main global economic institutions can already begin investigating its usefulness and use, as well as start the first prototypes.
However, in a decentralized trust system, those central entities are not necessary.
The initial blockchain and Bitcoin community proclaimed since the beginning that this technology would be disruptive, changing a lot of aspects of society. These changes will come with new ways of offering marketing services (and not only marketing) that the blockchain will enable, as the Internet did, and that are enough to write several posts.
Finally, I’ll quote the IBM Blockchain Vice President, Jerry Cuomo:
“We applaud judicious caution, but, at the same time, we believe that organizations and institutions that don’t quickly assess the potential of blockchain and begin experimenting with it risk falling behind as the world undergoes what we see as a tectonic shift.”
I’ll leave you anticipating a second post, where I’ll write about the applications in cybersecurity that the blockchain is already making possible.
References:
