 The widespread use of devices connected to the network, such as cars, medical equipment, industrial controllers (PLCs), appliances, etc., has brought with it a new and extremely vulnerable landscape.
The widespread use of devices connected to the network, such as cars, medical equipment, industrial controllers (PLCs), appliances, etc., has brought with it a new and extremely vulnerable landscape.
While there has been a breakthrough in connectivity issues (Twitter is everywhere!), the security issue has also been set aside. This is mainly due to the fact that for most users and organizations, Internet security is not a fundamental factor, which is why cases such as Mirai, one of the largest distributed denial of service attacks that has been recorded so far, which is just one of the first cases that we have to face in this new scenario..
The proliferation of interconnected devices has brought many advantages to users (homes, organizations): flexibility, mobility, automation, efficiency, etc., but what happens when we do not take the appropriate security measures and are unprotected by default?
You will then see how a series of small weaknesses can lead to a large leak of information, compromising personal, financial and confidential data, both private and organizational.
The device we are going to analyze is a Lacie MediaCenter, used mainly to download and save movies or photos, and then watch them from our PC, Smart-TV, Play, Xbox, etc. These devices (NAS) can store all types of files on a disk connected to the network, take an IP address and provide services such as SMB, AFP, FTP, SFTP, HTTP, HTTPS, BitTorrent, DNLA, UpnP and Windows Media Server.
And of course, to ensure maximum flexibility, we recommend that we activate the UpnP protocol in our router, which is not new, since video game consoles require it to play over the Internet. This allows, among other things, performing an inverse NAT using the IGD protocol. That is, the device can tell the router “Hey, open the X port so that the Internet can communicate with me”, then the router adds that rule to its redirection table.
In addition, if we want to access our photos from last summer from anywhere and at any time, the device gives us the possibility to configure a username (johnnyjumpup) to be able to identify it later.
To access our photos simply go to http://mynas.lacie.com/johnnyjumpup, which will redirect to our public IP address and a random port (configured automatically by the NAS), showing an access form over HTTP Or HTTPS, so we can access from the Internet to our device hosted in the local network, skipping the perimeter border.
 Figure 1 Web access to the NAS
Figure 1 Web access to the NAS
These configurations are made through a Wizard, so at no time do we find out what this device is performing below. Well, we already have access from the Internet to a NAS device hosted on a local network, and now?
It has been detected that, when browsing by user name, it provides us with information that would serve to identify the IP address, but also the site where these devices are located, which already gives us clues of other things that we will see next. To verify this, we took a dictionary with the most commonly used usernames, in order to obtain public IP addresses that published a NAS on the Internet. As proof of concept a dictionary was used with approximately 40000 user names.
As a result, we obtained a sample of 672 IP addresses that have one of these devices exposed to the Internet, ie: 672 homes / businesses have this device posted on the web, exposing access to their local network. These IP addresses were then used to identify the countries that most used these devices, with the United States having the largest number, with a total of 107. In Spain, 42 were identified and in Colombia 9 devices were identified. It is noteworthy that this quantity is sample, so the actual quantity is much greater. Below is a graph that reflects the sample amount of identified devices.
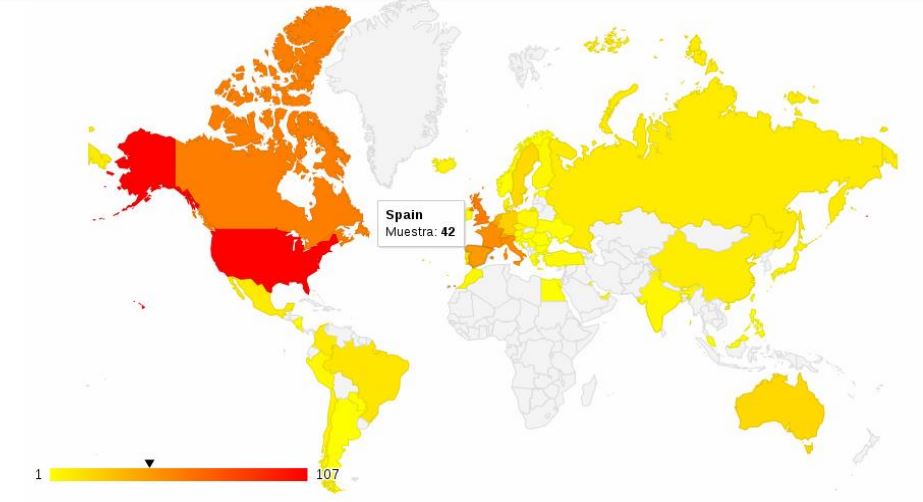 Figure 2 Geographical distribution of NAS – Lacie- Seagate
Figure 2 Geographical distribution of NAS – Lacie- Seagate
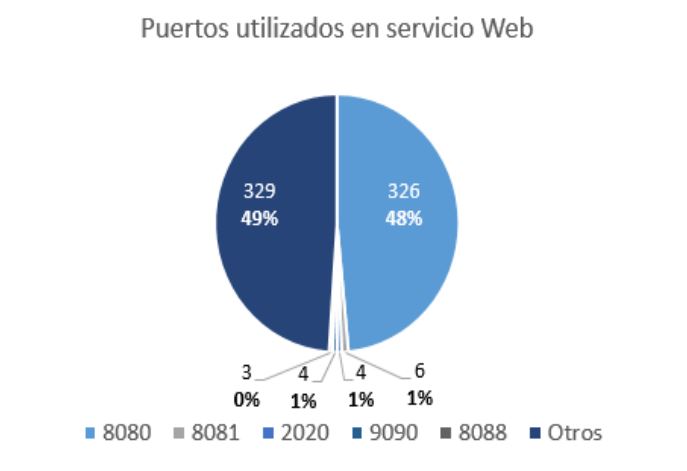
By making a calculation, it was identified that 49% of the sample uses port 8080, and the remaining 49% uses non-common and random ports, without a common pattern among them.
 After obtaining the list of IP addresses that have an NAS device, it is observed that most have port 21 open (FTP), so one can check if the anonymous user is enabled, and … surprise!
After obtaining the list of IP addresses that have an NAS device, it is observed that most have port 21 open (FTP), so one can check if the anonymous user is enabled, and … surprise!
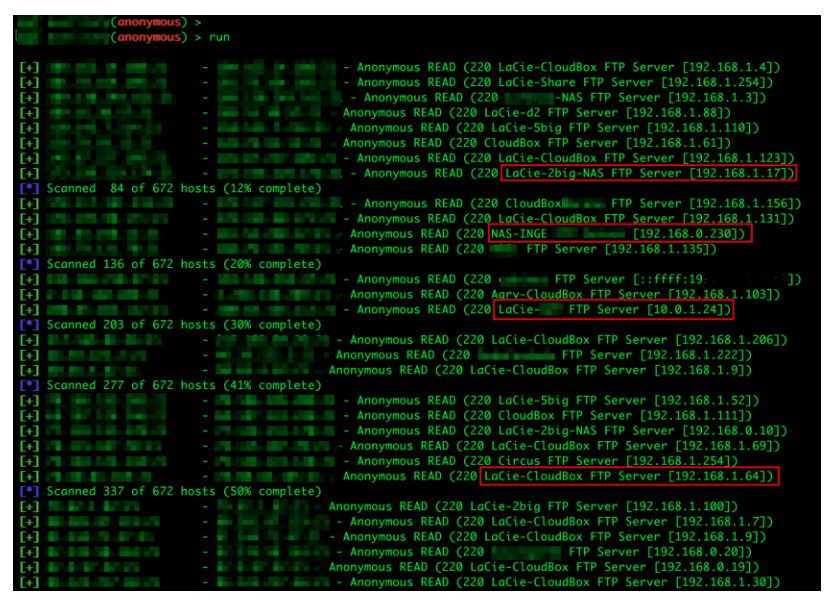 Figure 3 Anonymous Test User
Figure 3 Anonymous Test User
20% of the 672 devices have the FTP service active and the anonymous user enabled, that is, 134 devices are exposed to the Internet.
Another interesting aspect of the test was to note that when making FTP requests to the NAS, it responded by indicating the IP address of the internal network, which confirms that not only in local networks of households, but also in much larger networks as companies or universities. Although we have not investigated the devices found, it is expected that more than one will store personal data and sensitive corporate information, affecting the confidentiality of user information (leaving aside other more dangerous operations).
This analysis has shown that we are not very careful when using these devices in our homes, and that wanting to be at the forefront of technology, we are leaving aside aspects of security that put our personal and financial information at risk. Imagine that it was not a hard disk in the network, but the camera in our baby’s room…
Nor do organizations escape this type of failure, as both universities and companies have been identified. In light of this, it is not uncommon for information to be leaked almost every day, since, as you have seen, a sophisticated attack has not been necessary, just the right pieces and enough time.
In short, the arrival of the Internet of Things poses new challenges for both consumers and manufacturers, so there must be a joint effort in which manufacturers design devices with minimum security guarantees, and on the other hand users should be aware of the use of new technologies and the best measures to ensure their information.
(Further information can be obtained from the following paper, published in June 2016: FTP: The Forgotten Cloud, which mentions something as creepy as “there are still more than 13 million FTP servers in the IPv4 address space, 1.1 million of which allow “anonymous” (public) access. These anonymous FTP servers leak sensitive information, such as tax documents and cryptographic secrets. More than 20,000 FTP servers allow public write access…“).
