After what was seen in the first post of this story in this one we will keep telling you what happens and we will meet the boss. Put yourselves again in that situation that Johnny told us about in the first part.
“Hello, allow me to introduce myself. I’m John, Johnny’s boss. I am aware that I have many enemies among which are surely my competitors or even my own employees. Physically, no one can touch me, I always go with my bodyguards. But technologically, anyone could try to attack my team with the objective of stealing valuable information”.
That’s why, in addition to the corporate antivirus, I decided to add one more layer of security on my computer with Sysmon & Wazuh.
Sysmon, is a customizable monitoring tool for Windows systems with the ability to record events of system activity.
To install Sysmon, once downloaded, I opened a console with administrator permissions and executed the following command:
C:\Users\Pepote\Downloads\Sysmon> Sysmon64.exe –i sysmonconfig.xml –accepteula
It is highly recommended to install Sysmon with a configuration file that only records events of the activity that interests me, otherwise, it can fill the disk with legitimate activity records of my system.
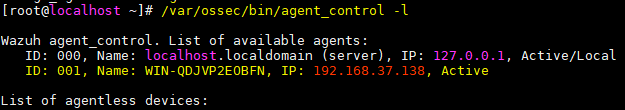
On the other hand, I installed the Wazuh service on a server, a fork of HIDS Ossec, which is an open source and free host-based intrusion detection system. And, to this server, I added my machine:
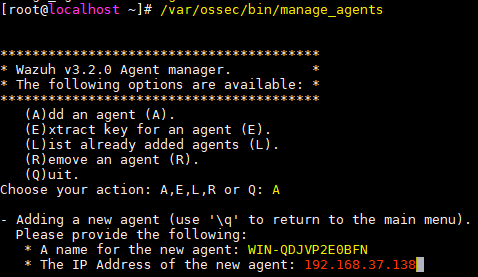
And I extracted the agent key from my computer, since I will need it to configure the Wazuh agent in my system:
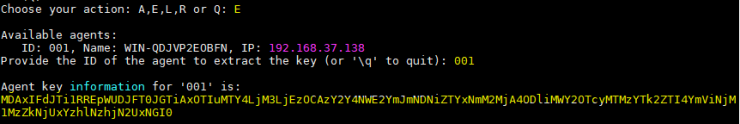
With this key, I went to my computer, I downloaded the Wazuh agent, I installed it and I added the IP of my Wazuh server and the agent code of my computer, generated previously:
I pressed “Save”, and before executing the agent, I went to the “View” tab and clicked on “View Config”. This is the Wazuh configuration file of my computer, where I added the following lines so that the agent also sends the events generated by Sysmon to the server:
<localfile> <location>Microsoft-Windows-Sysmon/Operational</location> <log_format>eventchannel</log_format> </localfile>
I saved the file, and then I ran the agent from the “Manage” tab and by clicking on “Start”.
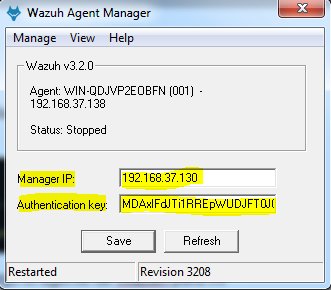
To verify that the agent was installed correctly, I could look in the logs of the agent itself, in the “View> View Logs” tab, or in the server executing the following command:
At that point, my computer was already sending events to the server and generating alerts according to the loaded rules. For my part, I created some additional rules to detect suspicious activity in the events generated by Sysmon:
<rule id="184778" level="12"> <if_group>sysmon_event1</if_group> <field name="sysmon.image">powershell.exe</field> <field name="sysmon.commandline">-nop -w hidden</field> <description>Sysmon - Ejecucion de Powershell sospechosa 1</description> </rule> <rule id="184779" level="12"> <if_group>sysmon_event3</if_group> <field name="sysmon.image">powershell.exe</field> <description>Sysmon - Conexion de red detectada desde Powershell</description> </rule>
I forgot, Wazuh also allows us to visualize the alerts generated in a graphical interface using the ELK stack (Elasticsearch, Logstash and Kibana).
So, before finishing my workday, I always go into the web interface to see the alerts generated on my computer and act quickly if a possible intrusion is detected:
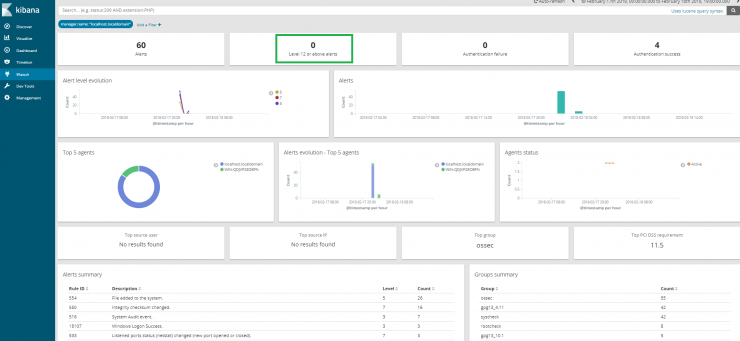
I do not see any high alert, level 12 or higher (highlighted with a green box in the previous image), so I can go home with no worries.
By the way, my WinRAR license has expired so I’m going to ask Johnny to find me a similar but free software.
(N.d.E.: In the next few days we will publish the third and last part of this interesting story).
