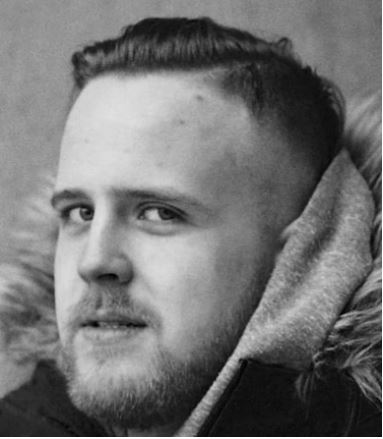
 Today’s post is authored by Robert Mardisalu, co-founder & editor of TheBestVPN.com, a computer security professional, privacy specialist and cybersecurity writer.
Today’s post is authored by Robert Mardisalu, co-founder & editor of TheBestVPN.com, a computer security professional, privacy specialist and cybersecurity writer.
He has written for many insightful blogs that help readers to think beyond the surface.
Every new year presents new cybersecurity issues and challenges for organizations. Skimming through the latest cybersecurity statistics will show how much of a threat cyberattacks pose. Handling information means you are charged with ensuring its availability, confidenciality and integrity against attackers, and be ready for the possible threats it may face.
In order to determine whether your organization is prepared to face these threats, you need to assess its cybersecurity readiness. This guide will help you do just that.
Cybersecurity Knowledge and Awareness Training
Your organization can have the best cybersecurity tech but that’s only half of the puzzle. The other half lies in the people actually involved with your organization. This includes employees, contractors, and third-party vendors.
It’s safe to say that many cyber attacks can be prevented if the target’s employees didn’t fall for phishing emails. According to PhishMe’s research, 9 out of 10 cyber attacks can be traced back to a phishing email. The problem here is that employees aren’t actively looking to get phished but still fall for this attack either due to negligence or lack of knowledge.
Why Cybersecurity Knowledge and Awareness Training are Important
There are many reasons why cybersecurity knowledge and awareness training are Important. The following are just some examples:
- Remote work/Telecommuting. Thanks to mobile and cloud technology, more and more companies around the world are implementing work-from-home policies. Employees formed to implement the best cybersecurity practices can help avoid attacks despite being hundreds of miles away.
- Government regulation. Being part of an organization, you should already be aware of the different regulatory bodies affecting your organization’s industry. Whether it be the US HIPAA, EU GDPR among many others, odds are routine cybersecurity awareness and training is required.
- The Internet of Things. Being in the age of the IoT means organizations and their employees need to quickly adapt to its expanding landscape. Employees have to be made aware of the vulnerabilities that their personal devices present.
Chief Information Security Officer (CISO)
A Chief Information Security Officer is the senior-level executive within an organization. They’re responsible for establishing and maintaining the enterprise vision, strategy, and program to ensure information assets and technologies are adequately protected. They are in charge of such responsibilities such as the following:
- Establishing cybersecurity policies
- Draft training and cyber risks awareness plans for employees
- Formulate incident response plans
Why a CISO is Important
Having a CISO means your organization has skilled personnel to lead the cybersecurity strategy and implementation for your business. This means that you won’t have to worry whether your organization’s cybersecurity is up to par — you can leave this responsibility up to your CISO.
Cyber Risk Assessment
Most organizations today rely to some extent in technology to support and perform its regular business. Whether your organization is an SMB, a global enterprise, or a non-profit, odds are that you use information systems and information technology for your daily processes, and in this scenario, cyberthreats pose an important challenge, because of their capability to disrupt business mission and operation. Cyberthreats, in brief, represent as risks for the organization, what makes it critical to determine which risks your organization may face. This is done through a cybersecurity risk assessment.
Defining Risk
There are many perspectives when regarding risks, but reputational, financial and operational loss are some of the most important. It can be measured as quantitative (e.g. in dollars or euros) or qualitative (e.g. very low, low, medium, high and critical). Risk vulnerability assessments involve three factors:
- Identifying the threat.
- Determining the system’s vulnerability.
- Determining the impact (reputational, operational, financial damage) if breached or incapacitated.
What is a Cyber Risk Assessment
According to the NIST Special Publication 800-30 rev1, risk assessments “are used to identify, estimate, and prioritize risk to organizational operations (i.e., mission, functions, image, and reputation), organizational assets, individuals, other organizations, and the Nation, resulting from the operation and use of information systems.”
Assessing your organization’s cybersecurity risk is crucial to keeping your organization safe from possible threats, and lets you understand, manage, control, and mitigate them. This involves a process of identifying, analyzing, and evaluating risks to ensure that your organization is ready for them.
When it comes to an information security risk assessment, you can ask questions such as the following:
- What are our most important information technology assets?
- What type of data breach (malware, cyber attack, or human error) would have a major impact on our business? This is especially important when customer information is involved.
- What are the relevant threats and their sources?
- What are the internal and external vulnerabilities?
- How grave will our losses be if those vulnerabilities are exploited?
- What is the probability of exploitation?
- What cyber attacks, cyber threats, or security incidents could affect our ability to function?
- What is the level of risk we’re willing to take?
Answering these questions helps to determine exactly what you need to protect. Using the answers, you can then develop IT security controls and data security strategies to mitigate risk. To help you understand the information value of the data you aim to protect, these are some of the most important questions:
- What risk are we reducing?
- Is this the highest priority security risk?
- Is this the most cost-effective method to reduce this risk?
Answering these questions will grant you a deeper insight into your information risk process in the scope of protecting your organization’s needs.
Why a Cyber Risk Assessment is Important
Based on what you’ve read so far, it’s easy to find reasons the need to perform a cyber risk assessment:
- Long-term cost reduction. Needless to say, identifying potential threats and vulnerabilities and implement controls to prevent them limits the impact of security incidents, thereby, saving your organization money in the long run.
- Provides a template for future assessments. Cyber risk assessments require continuous updates to be effective. A job well done on your first one helps to build a repeatable process that someone else can assume in the event of staff turnover.
- Improved organizational self-awareness. Taking a closer look at your organization’s strengths and weaknesses grants a deeper understanding of what areas your organization needs to improve and invest in.
- Mitigates impact of breaches and other security incidents. Having controls in place to mitigate potential nasty personal data breaches means a quicker and more efficient response, and in last term less organizational costs.
- Improves communication. A well-done cyber risk assessment usually requires different departments and stakeholders working as a team which can improve organizational visibility and communication.
- It’s required for cyber insurance. Cyber insurance can help your organization stay afloat in case a data breach does ever happen, but that will require your cybersecurity preparedness to be assessed by a third party. Performing a cyber risk assessment may help to comply with this requirement
- Avoid regulatory issues. US HIPAA (Health Insurance Portability and Accountability Act), PCI-DSS or EU GDPR (General Data Protection Regulation) are some examples of public and private regulations that require a cyber risk assessment.
Who Should Perform a Cyber Risk Assessment
If your organization is large enough, you should already have in-house personnel equipped to handle the process. This personnel usually consists of the IT staff, who understand how your IT infrastructure works, and the executives, who possess the knowledge about business processes and information flows. Unfortunately, smaller organizations may lack this in-house personnel. They may need to outsource this responsibility to a third-party, that can come in the form of a different company, individual consultants, or cybersecurity software.
How a Cyber Risk Assessment is Performed
Before commencing risk assessment and mitigation, you have to determine what data you have, what infrastructure you have, as well as the value of the data you’re trying to protect. An initial data audit may be needed for you to answer the following questions:
- What data do we collect?
- How and where are we storing this data?
- How do we protect and document the data?
- How long do we keep data?
- Who has access internally and externally to the data?
- Is our data storage location properly secured?
If you’ve already done a data audit for GDPR compliance, you’re already one step ahead. You’ll then want to define your assessment parameters by determining the following factors:
- The purpose of assessment
- The scope of the assessment
- The priorities or constraints that could affect the assessment
- The level and type of access required to get all the needed information
- The risk model your organization uses for risk analysis
These factors will help you determine what you’ll be analyzing, who has the expertise to perform a proper assessment and are there any regulatory requirements or budget constraints you need to be aware of.
Once you’ve determined all of that, you’re ready to commence the cyber risk assessment through the following steps:
1. Identify and prioritize essential assets
Depending on your budget, time and experience, you may want to limit your scope to the most essential assets. You can save time by defining a standard for determining asset criticality through which you can then classify each asset as critical, major, or minor. Take into account asset value, legal standing, and business importance.
2. Identify threat sources and threat events
The NIST defines a threat as “an event or condition that has the potential for causing asset loss and the undesirable consequences or impact from such loss.” For our purposes, we will consider two types of threats: adversarial threats (individuals, groups, organizations, or even nation-states) and non-adversarial threats (natural disasters, system failure, or human error). By identifying potential actors, you can now list every potential attack, exploit, glitch or mistake that you can think of, classifying them into one of the two categories (adversarial and non-adversarial).
You may want to start using some of the existing threat catalogues provided by some worldwide cybesecurity organizations, such as NIST or ENISA, and then customize it to your needs.
3. Identify vulnerabilities and the conditions needed to exploit them
You should have built up a list of everything that could happen up until this point. This next step moves away from the hypothetical into reality. Here you’re measuring the threats against your actual IT infrastructure and organization security implementations to determine their severity. You’ll need to determine what vulnerabilities coincide with what threats, and then factor in what — if any — controls are in place to mitigate such an event. You can identify vulnerabilities through any of the following:
- Vulnerability analysis
- Audit report
- The NIST vulnerability database
- Vendor data
- Incident response teams
- Software security analysis.
4. Identify the likelihood for those attacks to succeed
You’ve identified the possible threats and how they apply to your organization’s infrastructure, it’s time to determine how likely these attacks and events actually are as well as their potential for success. Here you base the likelihood of an attack being initiated on the capabilities of the attacker(s), their intent, and who they have historically targeted.
5. Identify the potential of impact
If you’ve followed the prior steps, you’ve basically put together your organization’s threat model. Now it’s time to determine the impact any of these events would actually have. As always, split them up into different categories such as harm to operations, assets, individuals, data subjects, third-parties, or even the nation.
6. Determine your organizational risk
Ultimately, your risk is going to be determined by the convergence of an event’s likelihood and the potential impact it poses. To calculate this, you can use any of the following methods:
- The scales provided by NIST
- Assigning numbers to likelihood and impact
- An alternative methodology that is supported by your industry or a regulatory body
7. Define your organization risk appettite
Once you have identified the main risks your organization poses, it’s time to do something to prevent them from happening or reduce the impact if the risks materializes. First, you need to determine which risks you are willing to accept, taking into account that risk mitigation comes at a cost. Because that, you will need to find a balance between your risk exposure and your budget.
The golden rule is: do not spend more money to protect an asset that its worth for your organization (remember, not only in direct financial terms, but also in operational and reputational costs, i.e. indirect financial costs). You don’t want to spend $5000 protecting a laptop that is worth $500.
8. Identify, define and implement risk mitigation controls
At this point, we know a) which are our main/critical organization assets, b) the threats they are facing, c) the impact and likelihood of each risk (= the ocurrence of a threat on an asset) and d) which risks we need to mitigate, after a loss/benefit evaluation.
Now comes the final part: identifying and implementing the controls needed to mitigate those unacceptable risks, in order to protect our most critical assets from cyberthreats. This is probably the longest and hardest part, and will require commitment, resources and, in some cases, a great deal of imagination and patience.
Cybersecurity Response Plan
One of the last and most important actions to perform is to define and implement a cybersecurity response plan (a.k.a incident response plan), that provides the organization with a guide on how to react in the event of a security breach. It minimizes damage, reduces disaster recovery time, and mitigates breach-related expenses. When formulating a cybersecurity response plan, it helps to keep things simple with a checklist. A simple checklist ensures that it’s easy to follow when a security breach does occur. When thinking of the steps, ask yourself the following questions:
- What is your response methodology standard (like NIST)?
- Who will be involved in the threat response?
- Who launches the incident response plan?
- Do you have the contact information of those involved in the threat response?
- How will you work the incident?
- What defines an incident?
- What classifies an incident as critical, high, medium, or low?
- What is the incident response workflow between those involved?
- When do you involve third-party retainers?
Cybersecurity awareness, risk assessment or cybersecurity response plan are complex and long projets by themselves, that require several iterations to reach maturity, but we expect this information will help you to give a step ahead to assess and improve your cybersecurity capabilities to deal with the cyberthreats of today and the future.
Keep safe.
