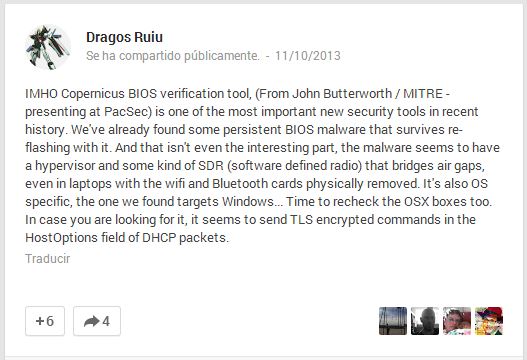
Two days ago, I had an e-mail in my inbox with this link. It seemed to be something serious, especially coming from Dragos Ruiu (@dragosr), the creator of the pwn2own contest, as he doesn’t need this kind of thing in order to be famous or make a name for himself. After reading it, I was a little bit scared.
As there isn’t a lot of information or an “official” report about this, I will give you some facts about his research and his findings:
- He found a malware that infects hardware.
- He found it installed in some laptops with Windows systems installed, but it proved to be somehow platform independent as it can infect a BSD system and OSx is not immune.
- It reflashes the system BIOS, and it is resilient: even after flashing the BIOS with a legit firmware, it will still be there. This forces the researcher to use a new machine for each test.
- It uses communication via SDR (Sotftware Defined Radio) to bridge air gaps (computers out of the network). It works even if the wireless and Bluetooth cards are physically removed.
(https://plus.google.com/103470457057356043365/posts/exuXRz5C3L3)
- It loads a Hypervisor.
- When the BIOS is infected, it doesn’t let you boot from external devices regardless of settings. Most of the times, it goes for internal disk.
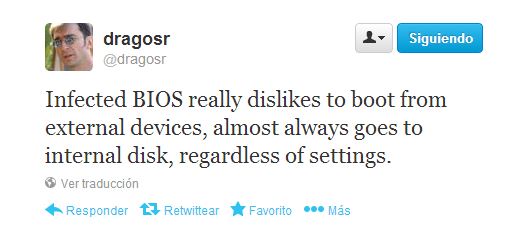
(https://twitter.com/dragosr/status/388632113496350721)
- It reflashes all USB drives plugged into an infected system, including external USB CD drives. It doesn’t affect the files in the USB, it directly infects the firmware.
- Just plugging an infected memory stick in a clean system will infect it… without even needing to mount it!
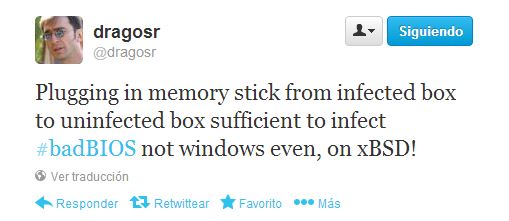
“I didn’t even mount the volume and it was infected.” (https://twitter.com/dragosr/status/393021493149302785)
- It bricks the USB drives if you eject them unsafely, but they come back to life when you plug them in an infected system.

https://twitter.com/dragosr/status/393026712197279746)
- In infected Windows systems, some extra .ttf and .fon files appear – three of them (meiryo, meiryob, and malgunnb) have a size that is bigger than expected.
- When trying to extract those files, they disappear from the burnt CD.

- People are pointing to Russia as an origin of this malware as they are the only known developers of reset flash controllers’ software. The malware also blocks the reflashing Russian software sites.

(https://twitter.com/dragosr/status/393023050750234624)
- The first symptoms were found in a Macbook, 3 years ago.
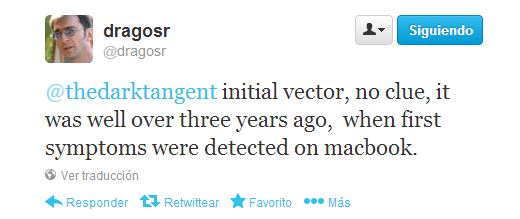
(https://twitter.com/dragosr/status/394223528813146112)
- A list of the md5 of files was uploaded to this link.
Right now, I don’t know if this could be maximum trolling, or not. I personally don’t think Dragos would play with his reputation like this. If we are facing a new kind of threat, we will need to be prepared for it.
What’s worse, until today there’s no clue of what the malware purpose is. I’ll try to keep you posted, and I highly recommend you to follow @dragosr and the hashtag #badBIOS on twitter in order to be updated about this topic.
[NOTE] If you are interested in a sample, keep an eye on malware.lu. @xylit0l posted this in kernelmode.info:
Re: New Bios Malware by Xylitol » Sun Oct 13, 2013 9:23 pm Talked to r00tbsd over irc, he have an image of the infected bios but got no time for the moment to add it on malware.lu.
Sources:
[1] https://plus.google.com/103470457057356043365/posts/9fyh5R9v2Ga
[2] https://plus.google.com/103470457057356043365/posts
[3] https://www.wilderssecurity.com/showthread.php?t=354463
[4] https://www.security.nl/posting/366329/Onderzoeker+ontdekt+mysterieuze+BIOS-malware
[5] https://kabelmast.wordpress.com/2013/10/23/badbios-and-lotsa-paranoia-plus-fireworks/
[6] https://twitter.com/dragosr
[7] https://twitter.com/rich_addr
[8] http://www.kernelmode.info/forum/viewtopic.php?f=16&t=2998&p=21195&hilit=BIOS+malware#p21195

— UPDATE —
I forgot to mention that there is a procmom dump, if you want to analyze it:
https://twitter.com/dragosr/status/393448446171963392
— ACTUALIZACIÓN —
Se me olvidó comentar que hay un dump de procmon, por si queréis echárle un ojo:
https://twitter.com/dragosr/status/393448446171963392
Link to twitter is broken, should be https://twitter.com/Xylit0l
Edited and corrected. Thank you.
There is another article that says this is all bull, that this isn’t even possible. Unfortunately I don’t understand enough about this topic to judge, but here goes the link:
http://www.rootwyrm.com/2013/11/the-badbios-analysis-is-wrong/
@Odom that guy (Phillip Jaenke) has a point, and he gives some good reasons to think it’s not a BIOS malware. But he is not saying this is not a malware, even if this is something working at OS level, it is still impresive.
Anyway lets see what the time shows, Dragos is not showing any irrefutable evidence, but at least he has been delivering dumps and file dump diffs, other reverse engineers can check it now if they want (e.g. https://plus.google.com/103470457057356043365/posts/bop8ufrMp7s).
I have the same issue, all the same symptoms. I work in IT – I tried different things to remove it but it always comes back. Yes, I removed the bios battery, power, memory and it still comes back. I pulled the wireless card, bluetooth, etc., doesn’t matter, it still manages to reappear. It seems like someone has control of the system because it can’t be that smart!!! Example – changing registry and it disables the editor or it changes permissions and then you are unable to do anything. I managed to boot to a cd that cant be written to and can start to make changes but when I start to own the system it reboots. I’m actually on the cd OS now, this is really happening, but it just seems unbelievable; it must go out and contact a site or some person(s) that can watch what you are doing and start the process. I know crazy, but it’s happening, I’m not a beginner – been doing this for 20+ years. I’m not sure if the average person would even know. (I think my issue started via my android phone) Ok, I’ll check back later.
I have two workstations and a SQL server that have very and similar problems. I have 17 years of work experience, and this is the strangest type of problems I’ve seen first hand.
Check out the Experts-Exchange.com help request I posted for details that are very similar to this BadBIOS virus.
Experts-Exchange.com article title: BIOS Virus symptoms but isn’t CIH virus
http://www.experts-exchange.com/Hardware/Desktops/Q_28215145.html
Pues no me lo creo.
Un virus con esa capacidad de camuflarse y esconderse incluso en la bios del propio ordenador deberia de tener un codigo ultradepurado, y ya no hablemos de multiples plataformas, control de dispotisivos hardware directos, creacion de un pseudolenguaje para entenderse los unos con los otros, y todo eso en cuanto..4 Kb? porque la bios hay que dejarla que tenga lo que debe tener o si no no funciona…ni arranca el ordenador…
esto me huele a bulo barato barato.
y eso de que infecta OpenBSD y windows y Mac, vamos, tiene exploits de todos los sistemas pa dar y tomar… alucine..
vamos que NO ME LO CREO. quiero pruebas reales del tema y por favor.. si no estan seguros, no publiquen esto que la gente se lo cree.
Just an idea.
What if this virus(badBIOS) was send to us through the satellites(sound weaves) orbiting around our planet, let’s say by those who like to spy on us NSA/GCHQ (the golden 5 spying countries). To design such a monster you need monstrous skills therefore only people with experience and provided expensive equipment/materials can design it.
It’s a possibility.
Just saying.
Obviously badbios is from NSA
“The ANT developers have a clear preference for planting their malicious code in so-called BIOS, software located on a computer’s motherboard that is the first thing to load when a computer is turned on.”
“Another program attacks the firmware in hard drives manufactured by Western Digital, Seagate, Maxtor and Samsung, all of which, with the exception of the latter, are American companies.”
Source:
http://www.spiegel.de/international/world/the-nsa-uses-powerful-toolbox-in-effort-to-spyon-global-networks-a-940969.html
http://www.spiegel.de/international/world/catalog-reveals-nsa-has-back-doors-fornumerous-devices-a-940994.html
See also http://cryptome.org/2013/12/nsa-tao-ant-pdf.pdf
So the reason Phillip says “its all wrong” is not because its not possible, but because it has to target specific motherboards.
Well ya….which no one disputes. Which means its very possible, and very likely! All they need is to target that one machine first… We are not talking about a random drive by, unless of course you happen to own that model mobo. I’m not a “computer guy” but isn’t this just common sense?
I think you are trying to quell fears of bios vulnerabilities since you work in the field. But the fact is many of us know we have been infected with viruses in the bios. Its more common now then ever before with the newer bios’s since CIH, not less common at all! Not only to purposely ruin hardware, which many people do to either cover their trace or just for kicks, contrary to what some posters think(the only people who would never do that is law enforcement and spies for information)…. but also to control the O/S…I mean they can be flashed right from windows nowadays, of course they are more vulnerable. and its been going on for years, with no bad checksums and surviving reflashes…
Some posters have linked specific virus examples, and to blow them off as only affecting specific model mobos, is semantics. Point is its possible.
The other issue that people refuse to acknowledge, is that its also possible to acoustically transmit viruses. Even though some people in this thread have linked how phones can transmit info in this exact way.
Then the argument becomes its not practical in the real world because they have to be within 10 feet of each other, or that they will be in so small increments it will take a long time, etc… Well ya, probably true. But when we are talking about laptops in a computer lab or office environment, or coming in close contact with other O/s devices, its even more likely, And We all know some hackers are persistent enough to wait years if need be…
I also believe I have a had a virus I can’t get rid of, that I got one december many years ago. Its a horrible feeling. Since the first time my pc fried on christmas day, after a friend of mine went to jail for credit card fraud, I always felt it was the russians he was buying the cc numbers off of, and because I was talking with his associate on aim. Or other pc gamers I talk junk with online who get their kicks, I have been threatened many times and have even had my gaming confg files altered over the years by rival gamers.
Sometimes I think its the Recording industry, because the virus always seems to attack the dvd rom firmware first. DvD drives don’t last long in my household. We go through half a dozen a year on a couple pcs, and we don’t even use them that often. Sometimes it feels like the purpose is to destroy every piece of hardware on the computer, starting with the cdrom, then vid card (monitor as a bonus) then the mobo and cpu, even if it takes months or years…
Ever year around the holdays, is a nightmare. I dread this time of year.
Buying a new pc doesn’t help because they just get infected again. What is my family supposed to do? Stop using the internet? Keep our pc’s off between the months of november to january? Get all new computers and devices at the same time? Maybe even our fios boxes just to be safe? lol Thats the only thing that ends up not being practical in this story. Because I tell you, I’m so glad to see someone else with the same experiences….
Most American families I know are using phones only now, not only because they can carry them around easier, but because their pc is too bogged down or faulty and frustrating to use. We can no longer blame ignorant users, because it can happen to anyone, even by just browsing to the most legit website. NBC.com for example.
I’m so glad someone like Dragos, a well respected security professional, who has the balls to discuss something like this happening to him perosnally, something many people like me have felt for a long long time, and have been looked at like we were crazy for years. We are not alone now.
Obviously its about being targeted (not a pun) …And its more common then you think….Welcome to 2014.
This sort of hacking, as well as even creepier attacks on my person from some sort of LRAD device. Good luck man. I’VE nearly stopped using computers for quite some time now. Good luck friend.
If
This is amazing. Everything being described has been going on for almost 2 years on my domain. December of 2012 a nasty virus swept through the house infecting all computers and smartphones. All the screens of all the devices showed the same controls. Data was streaming from left to right horizontally on a kind of dashboard. It looked just like the stock market tickers. I couldnt convince my roommate or his 13 year old daughter to wipe their smartphones but they did allow me to attempt to wipe and reinstall the O.S. of the 4 computers. I too had major trouble trying to boot from disks and the simple freeware wiping programs and OS boot disks were taking 10 imes longer then they should. One of the laptops started sending lines of code in a pulse like fashion through the default screen of Derriks Boot@nuke. the code mentioned something of key presses being invalid and the Computrace somehow got enabled in BIOS. I found a script in my own laptop that had over 1000 lines of code all mentionibg remote access and when I tried to copy that script to cdr my diskdrive would not funtion whatsoever. I grabbed the nearest flashdrive and was able to copy the script with the bizarre remote code and i put it into an old unused laptop that had its wifi card removed and was able to pull up the 1000 lines of remote code to show my roommate. we sat there silent as we read all that. we both left the room and when I returned the laptop that had no wifi card had its internet connection l.e.d. lit up! I ran over to it and the l.e.d.’s showed it was connected by bluetooth. I looked around my room and found that my Apple I-phone was hotspotting the old laptop through bluetooth even though I had bluetooth locked out with a passcode. I started getting worried and when I went to shut off that old laptop a 2-d vector graphic image of an angry face appeared on screen with the caption: “This is MY account!” now hoorrified I pulled the battery and the powercord and then turned to my Windows laptop and hit F8 to restore and instead of the screen going to the different options of repair or safe mode the screen just had one sentence on it: “You can not opt-out.” I about soiled myself! I didnt know much about computers but I knew I was just reinfecting by hotswapping the usb and still having 2 smartphones that were not wiped will reinfect as well so I had to wait until everyone was gone to try and wipe my devices but just before the fresh operating systems were installed I would get a ping on my wireshark scans from my roommates cellphone when he would enter the house and almost immediatly my devices would reinfect. I started to read all that i could about computers and rootkits. my dvd-rom drive became unusable only 3 months of use out of it. Dell sent me a replacement drive it too failed in less than 4 months. it would read certain disks absolutly perfect but refuse to read brand-new store bought anti-virus disks even with dd or copy-cat. the system logs showed that a SECOND physical drive was installed and it confused Windows and the logs showed the kernel would assign the same unique ID numbers to bothe the drives. All the logs kept pointing to USB as the source of my problems but all my flash-drives were brand new store-bought…And thats when I learned about U3. Even though these flashdrives made by SANDISK were supposed to be obsolete and removed off shelves back in 2009 I had the misfortune of buying one. I studied all I coould about USB devices and I have now have a huge collection of rare obsolete software for creating CD rom emulating USB devices and even own 3 USB rubber duckys to emulate hid keyboard so that i may hopefully try and gain some insight into the 2 years of hell that I went through. I am hoping someone on this message board might recognise my description of the command and control screen of the virus that seemed as if it was attacking me in real time. Again there was streaming data from left to right in english and the window boxes were labeled and one of them was labeled: “locate friends” much like facebook would have. it used bluetooth and travelled through bluetooth to other devices. Sounds much like the flame virus. I was also coonected at least 3 times by RIPE.ORG under operation optomistic d.a.d. because of the duplicate ip address’ from when we were being attacked. i found a bunch of bizzare docs in the trash files of my linux system that were in latin one of which read: “The China I.P. deceit is residential, I am O.K. as far as Japan time goes..”weird stff like that which made me believe RIPE.ORG was hot on their tail but thaty just freaked me out more knowing I now had 2 hidden entities inside my poor machines. One last thing..etherape and other wifi sniffers would pick up a small blip from twitter about every 5 minutes but none of the 3 of us ever had used twitter and sure enough i found a file buried in my system that had a twitter account on it and i was able to glean a username from it. the account is still up but no activity since December of 2012 when I had all my trobles. the account looks like some kind of facebook malware: LAURA@LAW320 anyone have a clue what it was that took over my domain?