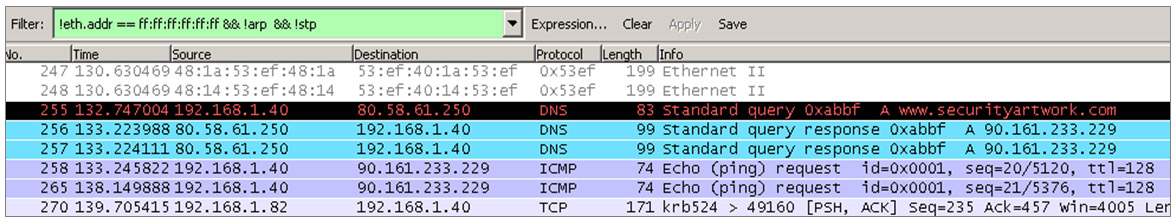
After reading @chemaalonso‘s post about DHCP Ack Inyector, I remembered my college years back in 2005 when you just needed to go to the library, plug-in your laptop to the network and voilà, just “listening” network traffic you saw all those vulnerable or misconfigured protocols such as STP, HSRP, DTP, etc..
Not only that. There wasn’t any type of control over the information the users could send, and using tools such as Gobbler, dsniff, ettercap, yersinia, etc., you could perform any man-in-the-middle attack. The most interesting part was that the networking devices used for traffic management were almost entirely Cisco. I.e. devices fully able to control and mitigate virtually most of these attacks, but that were configured to perform basic networking functions: routing, VLANS, ACL, QoS, etc. Either because of ignorance or carelessness, they were not being taken the performance that actually justified his acquisition.
Over time I have realized that this situation is quite common: it is really hard to find a company with strict configuration policies to secure the local network environment. I personally think that many organizations are unaware of the damage that a disgruntled employee could do in a network “poorly controlled”. Without using any sophisticated tools like Loki or Yersinia, it is possible to bring down an entire network with just a couple of packets. Using Scapy, you can perform MitM using ARP / DHCP / VRRP / HSRP or without much effort even more entertaining things like getting a pool of shells with Metasploit browser_autopwn and etterfilters.