As we have said, if until this year the GRU was one of the most opaque services in the world, in 2018 everything changes. Three facts stand out in the chronography, which conclude with the death of Lieutenant General KOROBOV in November; we will see in this section the first of them -and in the coming ones the other two, which occurred in the month of July.
On July 13, the US Department of Justice (DoJ) publishes [1], a document accusing twelve GRU agents – directly summoned by name and surnames – of possible Russian interference in the 2016 presidential elections. The person signing the document is none other than Robert Mueller, an advisor to the DoJ who coordinates investigations in this area – that of Russia’s relationship with the US presidential elections- and who, among other things, was director of the FBI for more tan ten years. After this accusation, the FBI includes among its “Cyber most wanted” the twelve agents of the service, highlighting that they can be armed and dangerous. Until then, the only Russian service that had the privilege of having agents among the most wanted by the FBI was the FSB. [Read more…]

 As we already mentioned in the
As we already mentioned in the  For a few months we have published a series of posts about Russian cyber intelligence in
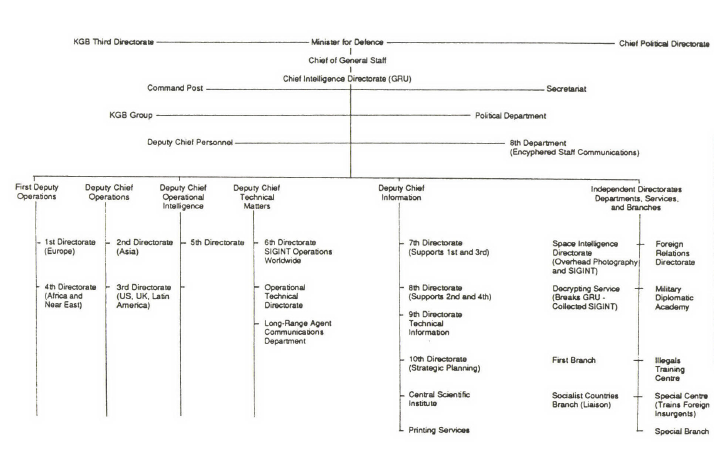
For a few months we have published a series of posts about Russian cyber intelligence in  The First General Directorate of the KGB was responsible for all operations of the service outside the USSR; this Directorate included departments focused on different geographical areas of the world, which were the operational nucleus of the General Directorate and were responsible, among other things, for the duties of almost all KGB-linked companies operating outside Soviet territory. And within these geographical departments, the Fifth was concerned with France, Italy, the Netherlands, Ireland … and Spain. Certainly we did not reach the level of the United States and Canada (First Department, exclusively occupied by these two countries) but we were not very far, perhaps on a second level. For different reasons that have obviously changed over the years, since the Civil War until now Spain has been a historical objective (not the most important, but relevant) for Soviet intelligence and now it is still so for Russian intelligence: from the NKVD during its lifetime to the current services, obviously passing through the KGB from the middle to the end of the last century. Exactly the same as the USSR, or Russia today, it also is and has been an important objective for the West: for example, we have only to read something about the operation Mari, in the 60s ([2]).
The First General Directorate of the KGB was responsible for all operations of the service outside the USSR; this Directorate included departments focused on different geographical areas of the world, which were the operational nucleus of the General Directorate and were responsible, among other things, for the duties of almost all KGB-linked companies operating outside Soviet territory. And within these geographical departments, the Fifth was concerned with France, Italy, the Netherlands, Ireland … and Spain. Certainly we did not reach the level of the United States and Canada (First Department, exclusively occupied by these two countries) but we were not very far, perhaps on a second level. For different reasons that have obviously changed over the years, since the Civil War until now Spain has been a historical objective (not the most important, but relevant) for Soviet intelligence and now it is still so for Russian intelligence: from the NKVD during its lifetime to the current services, obviously passing through the KGB from the middle to the end of the last century. Exactly the same as the USSR, or Russia today, it also is and has been an important objective for the West: for example, we have only to read something about the operation Mari, in the 60s ([2]).
 The relations of the Kremlin (by extension, of its intelligence services) with “classic” organized crime, with Russian mafias, is a fact more or less proven. Without going any further, in documents leaked by WikiLeaks the Spanish prosecutor Jose Grinda directly links the Russian mafia with the intelligence services of the country.
The relations of the Kremlin (by extension, of its intelligence services) with “classic” organized crime, with Russian mafias, is a fact more or less proven. Without going any further, in documents leaked by WikiLeaks the Spanish prosecutor Jose Grinda directly links the Russian mafia with the intelligence services of the country.