A few days ago while analyzing several emails I came across one that contained a suspicious attachment. It was a .docx document that at first glance had nothing inside but it occupied 10 kb.
A few days ago while analyzing several emails I came across one that contained a suspicious attachment. It was a .docx document that at first glance had nothing inside but it occupied 10 kb.
The mail had passed all the barriers, both SPF, as the two antiviruses that gateways have, and also the anti-spam filter.
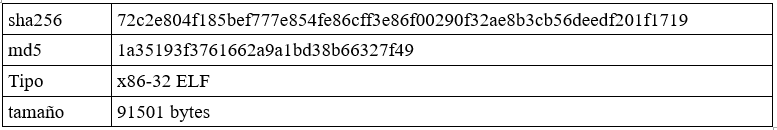
The .docx file can be treated as a tablet. Once extracted its content, I began to analyze all the files in the directory in search of domains or IP addresses that could be seen clearly:
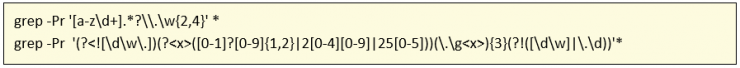
And I managed to find something interesting inside the path word/_rels/document.xml.rels where the following appears:
[Read more…]