(Please note this post was originally published in the Spanish version of Security Art Work last 26th Oct 2010)
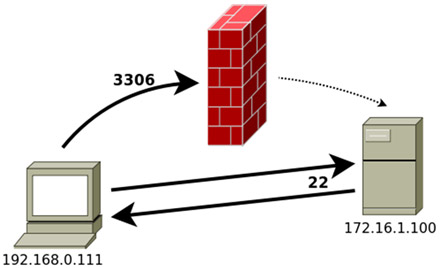
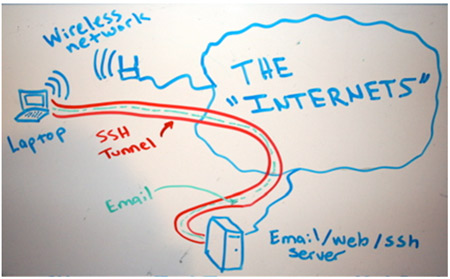
Covert channels is an evasion technique that allows an attacker to send information using the communication protocols headers. In this post we will cover-up of channels in the TCP/IP protocols and provide a tool, CovertShell, designed as a proof of concept. The sources are at the end of this post.
The TCP/IP protocol has headers that usually are initialized by the client to maintain or number a communication. The technique covert channels uses these fields to assign them values so the target machine does not interpret these fields as part of the communication, but to obtain data.
An interesting example was developed by Craig H. Rowland in his paper back in 1996: Covert Channels in the TCP/IP Protocol Suite, where he created a small client/server “CovertTCP” of no more than 500 lines that allowed file transfer between client and server, using for it only the fields SEQ, ACK (TCP protocol) and ID field (IP protocol). This information was on the protocol overhead and not in the payload.

 A couple months ago, our partner Jose Vila talked about
A couple months ago, our partner Jose Vila talked about  A couple of weeks ago I saw
A couple of weeks ago I saw