It is often admitted that ignorance is bliss. Conversely, another universal truth states that knowledge is power. I guess that we all have to find our place somewhere between both end members to keep our mental stability. However, when it comes to ICS cybersecurity knowledge is a must. The dark side lack of industrial processes know-how is the finger that plugs the hole in the dike, preventing the flood. But, as in the Dutch tale, this won’t last forever.
Security by obscurity paradigm is still firmly attached to many ICS managers’ views. This approach is absolutely unacceptable once you get even the slightest notion of the threat’s nature. Still, it is widely believed that the child will indefinitely keep on plugging the dike with his little finger.
Industrial processes knowledge and Stuxnet
Much has been said and written on Stuxnet, mainly because of its astounding refinement. However (please keep in mind that I’m an electrical engineer), what really shocks me is not its being the first malware specifically designed to attack an ICS, but the high degree of target’s physical processes knowledge involved.
Stuxnet was probably aimed to disrupt Iran’s uranium enrichment program. This material is used as fuel for nuclear power plants and in nuclear weapons construction. Uranium occurs in Nature as a mixture of two isotopes, 235U (lighter) and 238U (heavier). Natural concentration of 235U is under 1% whereas a concentration above 90% is required for military purposes (well over the 20% required for nuclear power plants). Enrichment process is usually performed inside centrifuges, machines that spin uranium gas at high speed. The heavier isotope experiences higher centrifugal acceleration and moves towards the spinning cylinder periphery while the lighter fraction (the useful one) remains by the rotation axis, where it is collected to be sequentially processed over and over again to reach the desired concentration. This is a very slow process because of the isotopes small atomic weight difference (3 atomic weight units to 238). In order to get enough material for the construction of a single device lots of time (or lots of money to provide a larger number of centrifuges) is required. To adjust the centrifuges speed frequency converters are used to drive the electric motors.
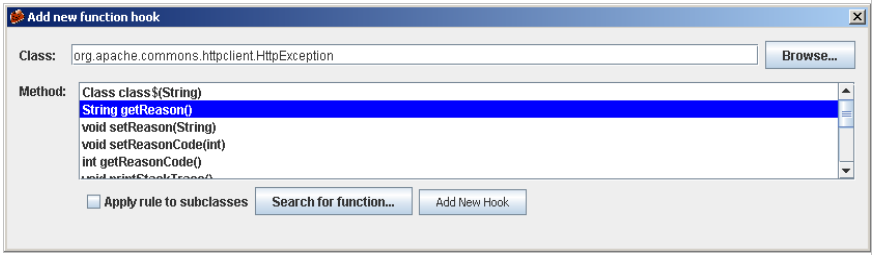
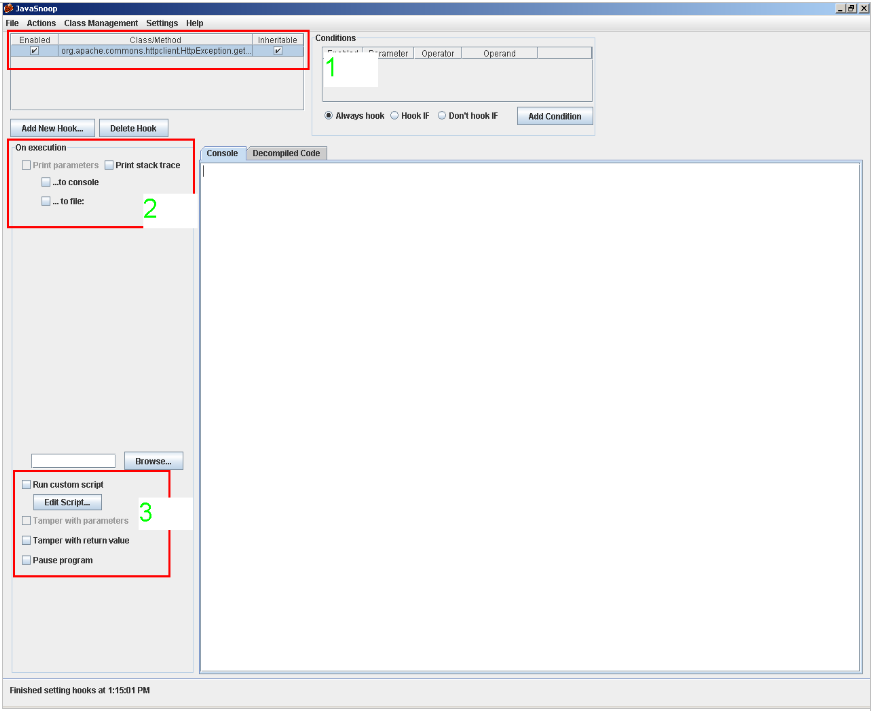
From this starting line, Stuxnet designers move on to tailor their strategy to the selected target: Iranian enrichment facilities. They tuned Stuxnet to pray on ICS with Siemens control systems (Simatic PLC and WinCC SCADA software) monitoring frequency inverters manufactured by Vacon (a finnish maker) and Fararo Paya (an iranian one). In addition, a number greater than 33 of this devices should be in place for the facility to qualify as a target. What is more, frequency settings should range from 807 Hz to 1,210 Hz (typical enrichment process settings).
Now comes my favorite part: choosing the attack mechanism. Once Stuxnet gains command and control of the system, it disrupts normal operation by forcing centrifuges spinning frequency (ie speed) to increase up to 1,410 Hz (above the maximum normal operation), then drop sharply to a value as low as 2 Hz (almost a complete halt, although machines rotating speed could depend on other factors), and then accelerate again to 1,064 Hz before returning to the normal operating sequence. This disruption repeats in predetermined cycles that involve, say, running at 1,410 Hz during 27 days, then a good dive down to 2 Hz and then 1,064 Hz again (resulting in good uranium shake) for another 27 days, and so on and on. This behavior does not affect all the devices in the same group, at least not simultaneously, but only a certain subset (to make malfunction detection harder, I guess). The goal is not only to disrupt the process. The goal is not to destroy the computer, or delete the program running on the PLC or any other action apparently definitive but, in practice, easily detected and fixed. These kind of actions would have warned the operator and the outcome would have been much restricted. It is obviously much more effective to cause the facility to produce uranium out of specifications for months for no apparent reason, something much more difficult to fix and therefore more harmful. The malware was intended to hide itself and its effects, so alarms logs and historians didn’t keep record of abnormal operation. Also, Stuxnet was able to reinfect a device in the event of original code being reloaded by the operators.
Lessons learned?
Beyond the initial shock (think of we poor ICS designers and operators and our broken safety feeling), there are some valuable lessons to be learned.
Much of the skepticism (real or fake) put up by ICS managers lays on their lack of understanding of the attack vectors and attacker’s goals. As far as they can see, a cyberattack is the digital equivalent of a carpet bombing, a blind and useless act of destruction. However, life ain’t that simple. As we can see from the Stuxnet case is that it is possible, given enough knowledge of an industrial process, to perform very sophisticated attacks aimed to cause much more damage in ways very difficult to fix: wastewater treatment plant discharges out of legal limits. An increase of non-compliant product resulting in economic cost and loss of reputation as it can be associated with missed deadlines or, worse, out-of-specs product reaching customers unnoticed (after all, statistical quality control samplings are designed to fit the ‘natural’ variability of our non disrupted process, so our standard sample size or sampling frequency may be inadequate to detect the situation). Or erroneous billing owing to altered data from meters (obviously up to destroy our reputation). What is worse, when we turn to our ICS it keeps telling that everything’s OK. And, let’s face it, how long will it take until you realize that maybe our control system has been hit by a cyberattack? After all, it is a risk that you have always dismissed…
You might regard yourself as a ‘good guy’. You have lots of friends, a good reputation and no enemies. But, even if that’s true, in a global market where processes and machinery are increasingly standardized, who can tell for sure that you will not be victim of malware designed to hit a third party who just happens to share equipment or methods with you? Just one example: centrifugal machines originally used in olive oil production are now used to dewater sludges from (waste or fresh) water treatment plants.
Too often I hear arguments like ‘our system is not connected to the Internet’. Aside from the healthy skepticism that such an statement shall raise, we must remember that Stuxnet was designed to copy itself, whenever possible, by means of portable devices such as USB memory sticks or those PC used to load projects to PLC.
What every engineer knows
A short time ago the information used in industrial process engineering was paper-based and access to it was very limited: technical books purchase, suppliers technical data provided by salesmen, documentation gathered in specific technical courses, and so on: photocopies, photocopies, photocopies. The Internet has changed it all. Today we have almost unrestricted access to highly detailed and specific documentation from our very desktop PC. I remember the time when every engineer kept large amounts of information in various media. This personal treasure contained much of our knowledge and ability to design and its loss was a risk we could not afford. Today that is no longer necessary. The Internet is the ultimate file: pdf, pdf, pdf.
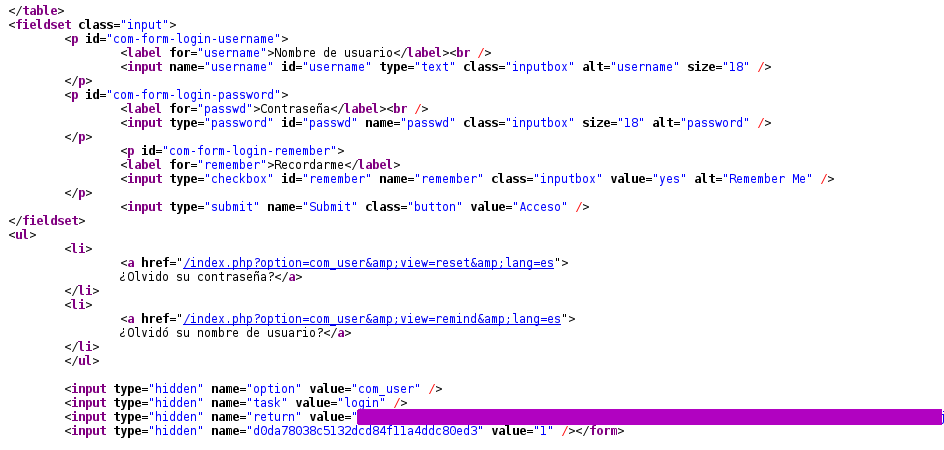
It’s amazing how much stuff about the processes and equipment in use in any given company lies out there, waiting to be discovered when appropriately searched. There is much more than technical documentation in the form of catalogs and data sheets. Providers often describe their references and success stories, sometimes in great detail, in multiple places: their websites, technical magazines, at conferences and fairs…The companies themselves sometimes release papers on their own state-of-the-art developments (or anything they are proud of). Constructors companies do just the same. When it comes to public infrastructures, Administrations grant tenders access to lots of detailed stuff. At least in Spain, some public projects are made available to every citizen to allow people to made allegations against the future infrastructure. You can find even undergraduate and post-doc academic works sponsored by companies regarded as critical operators: I have found academic papers describing the protocols and communication networks and control systems in real power grid substations of named companies. Sooner or later all this information makes it to the Internet.
Keeping this in mind, the next question is: do you really want to build your cybersecurity any longer on the idea that no one knows your industrial process?
Final note: specific data on Stuxnet and its performance is taken from the report published by Symantec (authors Nicolas Falliere, Liam O’Murchu, and Eric Chien) available here.